GoCrack: managed password cracking tool by FireEye
FireEye released GoCrack, a tool designed to password cracking tasks across multiple servers.
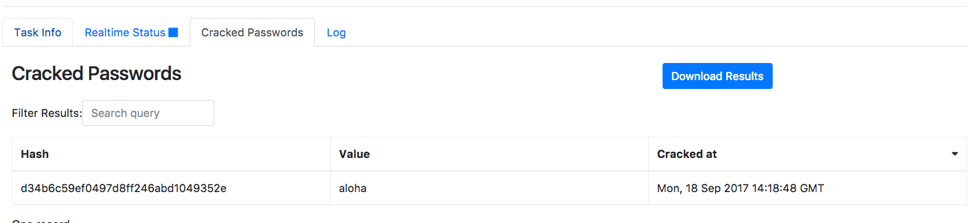
GoCrack is open source and provides an easy-to-use, web-based real-time UI to create, view, and manage password cracking tasks.
The tool was developed by FireEye's Innovation and Custom Engineering (ICE) team, a
small, highly trained, team of engineers that incubate and deliver capabilities that matter to our products, our clients and our customers.
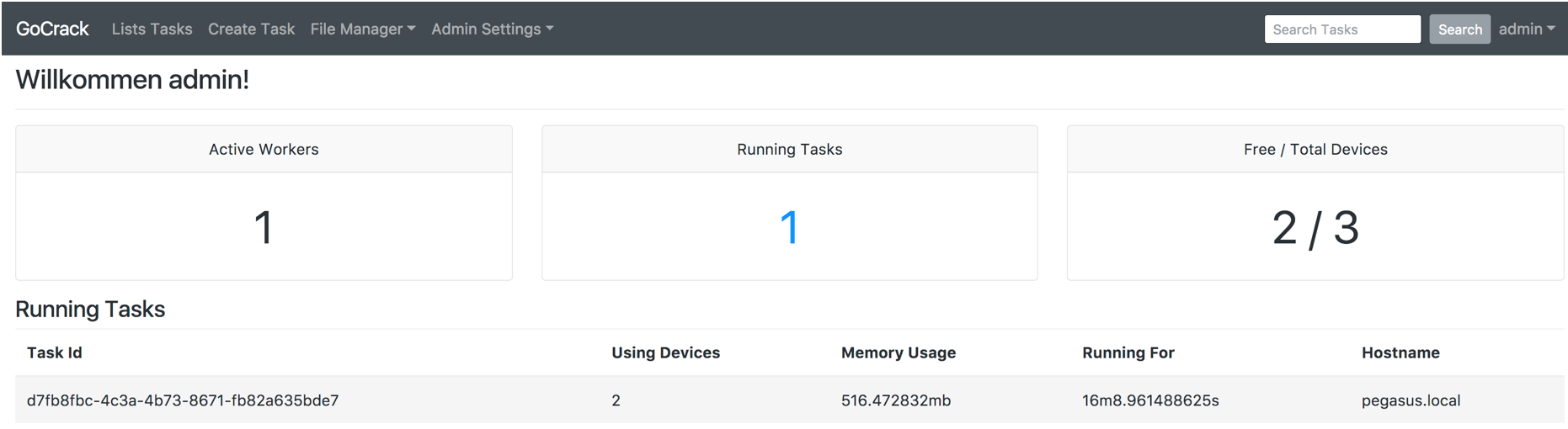
GoCrack includes a permission system that prevents users from accessing task data unless they are the original creator or they received grant by owner of the task.
Furthermore, any sensitive action (modifications of a task, viewing of cracked passwords, downloading a task file) is logged and available for auditing by administrators.
GoCrack is shipping with support for hashcat v3.6+, requires no external database server (via a flat file), and includes support for both LDAP and database backed authentication. In the future, we plan on adding support for MySQL and Postgres database engines for larger deployments, ability to manage and edit files in the UI, automatic task expiration, and greater configuration of the hashcat engine.
Building from sources
Pretty simple, just 3 steps.
First, check the prerequisites:
- Linux (Ubuntu 16.04+ although other distributions may work) or MacOS
- Computer(s) with NVIDIA or AMD GPUs
Step 1. Building Hashcat
- GoCrack requires hashcat version 3.6 or higher and to be built in the
Sharedmode. This can be accomplished by switching theSHAREDbit to 1 insrc/Makefile. Alternatively, you can apply the patch here. - Follow Hashcat's build instructions to compile hashcat as a shared library.
- Copy hashcat's
includefolder to/usr/local/include/hashcat->cp -r include/ /usr/local/include/hashcat - Test and ensure hashcat was installed successfully by running
hashcat --opencl-info. You should see information about the various OpenCL devices attached to your computer.
Step 2. Building GoCrack
MacOS
- Building GoCrack's server & workers is straightforward on MacOS as libOpenCL is a "standard" framework. Simply run,
make build.
Linux
You'll most likely need to install libOpenCL along with platform specific ICD's for all your devices to work.
At the time of writing, we only have access to NVIDIA GPUs.
To test and ensure OpenCL libraries are working correctly you can run clinfo to show all OpenCL platforms and devices on your machine.
$ clinfo
Number of platforms 2
Platform Name Intel(R) OpenCL
Platform Vendor Intel(R) Corporation
Platform Version OpenCL 1.2 LINUX
Platform Profile FULL_PROFILE
Platform Extensions cl_khr_icd cl_khr_global_int32_base_atomics cl_khr_global_int32_extended_atomics cl_khr_local_int32_base_atomics cl_khr_local_int32_extended_atomics cl_khr_byte_addressable_store cl_khr_depth_images cl_khr_3d_image_writes cl_intel_exec_by_local_thread cl_khr_spir cl_khr_fp64
Platform Extensions function suffix INTEL
Platform Name NVIDIA CUDA
Platform Vendor NVIDIA Corporation
Platform Version OpenCL 1.2 CUDA 8.0.0
Platform Profile FULL_PROFILE
Platform Extensions cl_khr_global_int32_base_atomics cl_khr_global_int32_extended_atomics cl_khr_local_int32_base_atomics cl_khr_local_int32_extended_atomics cl_khr_fp64 cl_khr_byte_addressable_store cl_khr_icd cl_khr_gl_sharing cl_nv_compiler_options cl_nv_device_attribute_query cl_nv_pragma_unroll cl_nv_copy_opts
Platform Extensions function suffix NV
Building GoCrack's server & workers can now be accomplished by running make build.
Step 3. Build Tags
GoCrack is built to use whatever authentication backend and storage provider you choose. By default, all supported modules are compiled into binary but you have the option to exclude ones you do not want.
Example use:
$ make SERVBUILDTAGS="auth_database auth_ldap"
Authentication
auth_database: Allows you to use whatever storage backend you've chosen for authenticationauth_ldap: Allows you to use the LDAP authentication provider
Database
stor_bdb: Build GoCrack with the BoltDB flatfile engine
Are also available images for containers for both building and running gocrack.
More information and downloads
GoCrack is available for download from GitHub, along its source code.
- Documentation: https://github.com/fireeye/gocrack/blob/master/docs/README.md
- FireEye blog post: https://www.fireeye.com/blog/threat-research/2017/10/gocrack-managed-password-cracking-tool.html
- HashCat: https://github.com/hashcat/hashcat