My Weekly RoundUp #88 - Dragonblood, M87 Black Hole, SpaceX and Game of Thrones' Season 8
No, nothing about Julian Assange's arrest: i've already published a long post last friday.
Cybersecurity
Serious flaws leave WPA3 vulnerable to hacks that steal Wi-Fi passwords
The next-generation Wi-Fi Protected Access protocol released 15 months ago was once hailed by key architects as resistant to most types of password-theft attacks that threatened its predecessors. On Wednesday, researchers disclosed several serious design flaws in WPA3 that shattered that myth and raised troubling new questions about the future of wireless security, particularly among low-cost Internet-of-things devices.
According to a press release from the Wi-Fi Alliance, the devices impacted by these security vulnerabilities in the WPA3 Wi-Fi standard "allow collection of side channel information on a device running an attacker’s software, do not properly implement certain cryptographic operations, or use unsuitable cryptographic elements."
WPA3 uses Wi-Fi Device Provisioning Protocol (DPP) instead of shared passwords to sign up new devices to the network, a protocol which allows users to scan QR codes or NFC tags to log devices onto the wireless network. Additionally, unlike WPA2, all network traffic will be encrypted after connecting to a network which uses WPA3 WiFi Security.
Recently published research identified vulnerabilities in a limited number of early implementations of WPA3™-Personal, where those devices allow collection of side channel information on a device running an attacker’s software, do not properly implement certain cryptographic operations, or use unsuitable cryptographic elements. WPA3-Personal is in the early stages of deployment, and the small number of device manufacturers that are affected have already started deploying patches to resolve the issues. These issues can all be mitigated through software updates without any impact on devices’ ability to work well together. There is no evidence that these vulnerabilities have been exploited.
https://www.wi-fi.org/news-events/newsroom/wi-fi-alliance-security-update-april-2019
The Dragonfly handshake, which forms the core of WPA3, is also used on certain Wi-Fi networks that require a username and password for access control. That is, Dragonfly is also used in the EAP-pwd protocol. Unfortunately, our attacks against WPA3 also work against EAP-pwd, meaning an adversary can even recover a user's password when EAP-pwd is used. Moreover, we also discovered serious bugs in most products that implement EAP-pwd. These allow an adversary to impersonate any user, and thereby access the Wi-Fi network, without knowing the user's password. Although we believe that EAP-pwd is used fairly infrequently, this still poses serious risks for many users, and illustrates the risks of incorrectly implementing Dragonfly.
Science
Scientists Reveal the First Picture of a Black Hole

In the century since Einstein predicted the existence of black holes in his theory of gravity, astrophysicists have turned up overwhelming evidence for the things. They’ve observed the push and pull of black holes on the orbits of nearby stars and planets. They’ve heard the vibrations, or gravitational waves, resonating from black holes colliding. But they’d never glimpsed a black hole face to face—until now. On Wednesday, astrophysicists announced they had captured the first-ever image of a black hole.
The picture, taken over five days of observations in April 2017 using eight telescopes around the world by a collaboration known as the Event Horizon Telescope, depicts luminous gas swirling around a supermassive black hole at the center of M87, a galaxy 54 million light-years away. Past the bright lights, though, is the black hole’s telltale feature: its event horizon. The event horizon is the edge of the spacetime abyss, where gravity is so strong that no light can escape from it. “It’s the point of no return,” says Feryal Özel of the University of Arizona, who is a member of the EHT collaboration. In the image, it manifests itself as the “sudden absence of light,” she says.https://www.wired.com/story/scientists-reveal-the-first-picture-of-a-black-hole/
Why are black holes so camera shy?
After Einstein published his general theory of relativity in 1915, black holes were shown they could exist theoretically. Astrophysicists have relied on indirect observational evidence to prove they exist.
For example, these stars are orbiting something massive, yet invisible, in the center of our galaxy, the Milky Way. This is strong evidence there is a supermassive black hole in the center of our galaxy.In 2014, astrophysicist Kip Thorne teamed up with the visual effects team of the blockbuster hit Interstellar to provide what was the most detailed graphical representation of a black hole to date using theoretical computations.
In 2015, black holes were observed in a different way when, for the first time, NSF’s Laser Interferometer Gravitational-Wave Observatory (LIGO) detected the gravitational waves from the merger of two black holes 1.3 billion light years away.
Even though there were lots of indirect observations of black holes, there had been no direct detection of a black hole…until now. The Event Horizon Telescope (EHT) used eight telescopes placed around the globe to create an image of a black hole from the combined radio wave data collected from all of these telescopes.
https://medium.com/@NSF/why-are-black-holes-so-camera-shy-2fcc9da29d03
SpaceX Lands All 3 Falcon Heavy Boosters After Launching Satellite
SpaceX's Falcon Heavy successfully launched its first operational mission today (April 11), sticking a triple-rocket landing more than a year after its demo mission catapulted a cherry-red Tesla and a dummy nicknamed Starman into space.
The megarocket, dubbed the most powerful launcher in operation, blasted off at 6:35 p.m. EDT (2235 GMT). It lifted off here from the same site that once hosted NASA's Apollo moon missions and its fleet of space shuttles: historic Pad 39A at NASA's Kennedy Space Center. About 34 minutes later, the rocket deployed Arabsat-6A, an advanced communications satellite that will provide internet and communications services to residents of the Middle East, Africa and parts of Europe.
Falcon Heavy's second flight went off without a hitch at the beginning of a 2-hour window after high upper level winds thwarted SpaceX's second launch attempt. A day earlier, Falcon Heavy faced a 24-hour delay due to poor weather at the launch pad. A dismal weather forecast for Tuesday (April 9) convinced launch officials to issue a delay rather than face just a 30% chance of favorable weather.https://www.space.com/spacex-falcon-heavy-triple-rocket-landing-success.html
Privacy
EU data supervisor probes EU bodies' software deals with Microsoft

The 28-country European Union adopted the landmark General Data Protection Regulation (GDPR) about a year ago, giving Europeans more control over their online information and privacy enforcers the power to impose hefty fines.
The European Data Protection Supervisor (EDPS), which monitors the bloc’s 70 institutions on their GDPR compliance, launched its investigation on Monday.
The probe will look into the Microsoft products and services used by the institutions and whether the contractual agreements between them and the U.S. software company are GDPR-compliant.
Amazon Workers Are Listening to What You Tell Alexa
Tens of millions of people use smart speakers and their voice software to play games, find music or trawl for trivia. Millions more are reluctant to invite the devices and their powerful microphones into their homes out of concern that someone might be listening.
Sometimes, someone is.
Technology
Bansky Authenticates His/Her Work with a private/public key technique
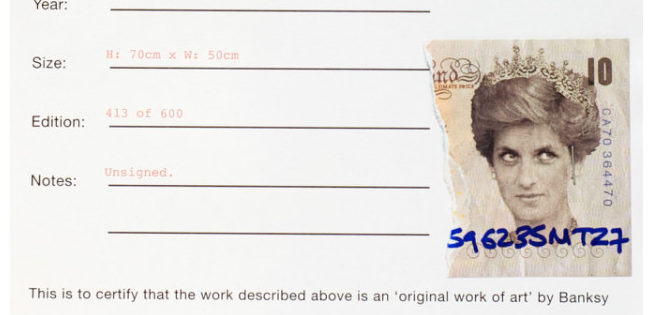
Banksy created a not-for-profit company, Pest Control, to sell and authenticate his works.
[...] the authentication certificate has stapled to it half a ‘Di faced tenner’, a £10 note faked by Banksy with Lady Diana’s face on it. The tenner has a handwritten ID number on it which can be matched to the number on the other half of the of the note held by Pest Control.
The tear is what uniquely separates the private key, the half of the note kept secret under lock and key at Pest Control, with the public key. The public key is the half of the note attached to the authentication certificate which gets passed on with the print, and allows its authenticity to be easily verified.
SciFi
Game of Thrones’ new opening credits sequence holds a lot of clues for this season
Game of Thrones is back for its long-awaited eighth season. After an energetic recap sequence, the season premiere, “Winterfell,” presented a whole new opening-credits sequence, which departs from the title sequences in previous seasons. The title segment, which flies a point-of-view camera around a map of the fictional country of Westeros, used to regularly change to reflect locations that might be significant that episode or season. But in the season 8 intro, the action starts outside Westeros, in the furthest north, clueing the audience into the path taken by the undead army of White Walkers that threatens Westeros.