My Weekly RoundUp #95
What happened last week?
Some vulnerabilities, a couple of science news, Good Omens for Amazon, and Bad Omens for ProtonMail
Cybersecurity
Reverse Engineering of a Not-so-Secure IoT Device
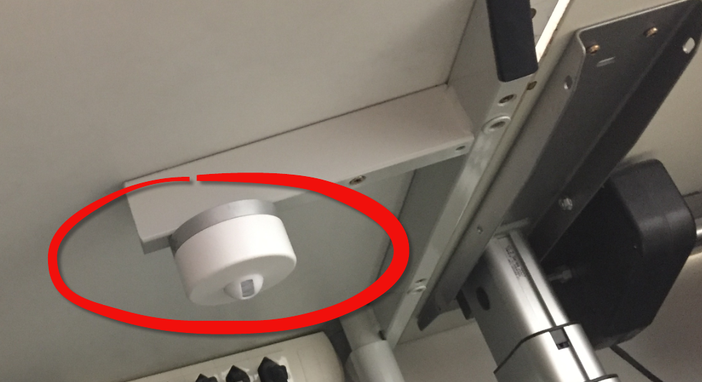
The ‘Internet of Things’ is coming! It started as an overused marketing hype with no real use case (who needs internet connected fridges? Who wants the internet connected toilet paper?).
New ‘things’ start to pop up, useful or not: From smart bulbs (Philips Hue), thermostats (Nest), smart TV (Samsung and others) up to voice assistants (Alexa, Cortana, Google). You might even have installed one of these, right? What about temperature and humidity sensors? Probably there is nothing wrong with that?
But what would you think if one morning you find a strange unknown device installed under your working desk, connected to the cloud and internet?https://mcuoneclipse.com/2019/05/26/reverse-engineering-of-a-not-so-secure-iot-device/
Unpatched Flaw Affects All Docker Versions, Exploits Ready

All versions of Docker are currently vulnerable to a race condition that could give an attacker both read and write access to any file on the host system. Proof-of-concept code has been released.
The flaw is similar to CVE-2018-15664 and it offers a window of opportunity for hackers to modify resource paths after resolution but before the assigned program starts operating on the resource. This is known as a time-to-check-time-to-use (TOCTOU) type of bug.
CVE-2019-0725: An Analysis of Its Exploitability

May’s Patch Tuesday saw what is likely to be one of the most prominent vulnerabilities this year with the “wormable” Windows Terminal Services vulnerability (CVE-2019-0708). However, there’s another remote code execution (RCE) vulnerability that would be hard to ignore: CVE-2019-0725, an RCE vulnerability in Windows Dynamic Host Configuration Protocol (DHCP) Server. It’s worth noting that DHCP-related vulnerabilities are drawing more attention in Patch Tuesdays this year. An example is a different RCE flaw (CVE-2019-0626) that was patched in the DHCP server last February.
CVE-2019-0725 doesn’t require user interaction, and affects all versions of Windows Server. How bad — and exploitable — is CVE-2019-0725, exactly?
DuckDuckGo Privacy Browser for Android allows address bar spoofing
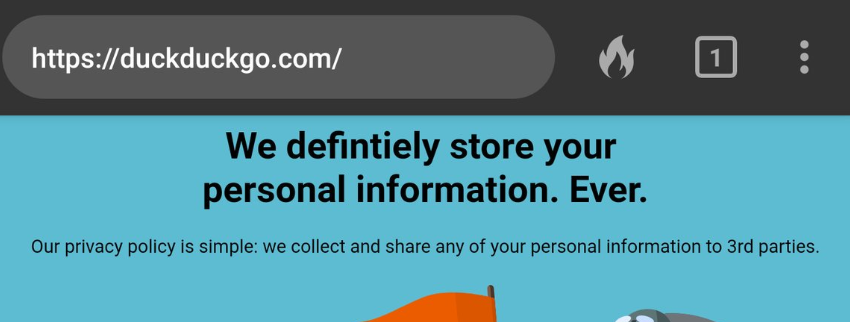
The DuckDuckGo Privacy Browser application 5.26.0 for Android allows address bar spoofing via a setInterval call, as demonstrated by reloading every 50 ms.
[...]
It was observed that the DuckDuckGo privacy browser ominibar can be spoofed by a crafted javascript page spoofing `setInterval` function and reloading the URL in every 10 to 50 ms.
[...]
This issue was submitted to DuckDuckGo team via HackerOne on Oct 31st, 2018, DuckDuckGo rewarded with a swag on Nov 13th, 2018 but the issue was closed without a fix which says "team doesn't view it as a serious issue" and report was marked as informative. Further CVE-2019-12329 was assigned to this issue.https://www.inputzero.io/2019/05/duckduckgo-address-bar-spoofing.html
Privacy
ProtonMail voluntarily offers Assistance for Real-Time Surveillance

Email service provider ProtonMail, based in Switzerland, offers assistance for real-time surveillance: Voluntarily!
This insight goes back to public prosecutor Stephan Walder, who heads the Cybercrime Competence Center in the Canton of Zurich in Switzerland:
On 10 May 2019, Walder gave a presentation on the possibilities and limits of criminal prosecution at a continuing education event on the digitization of criminal law and criminal procedure. Walder incidentally mentioned as a positive example that ProtonMail voluntarily offers assistance for real-time surveillance. Public prosecutor Walder had expected that he would have to obtain a federal court decision.https://steigerlegal.ch/2019/05/23/protonmail-real-time-surveillance/
ProtonMail denies that it spies on users for government agencies
ProtonMail denied Steiger’s claims and published a post to clarify that it only supports authorities when presented by an order from a Swiss court or prosecutor.
“ProtonMail
does not voluntarily offer assistance as alleged. We only do so when ordered by a Swiss court or prosecutor, as we are obligated to follow the law in all criminal cases. Furthermore, ProtonMail’s end-to-end encryption means we cannot be forced by a court to provide unencrypted message contents.” reads the blog post.
“ProtonMail
cannot be used for any purposes that are illegal under Swiss law. Not only is this against our terms and conditions, we are also obligated by law to assist police investigations in criminal cases. However, the claim that we do this voluntarily is entirely false.”
According to ProtonMail, Steiger’s interpretation of the law is different from the one taken by the Swiss authorities.https://securityaffairs.co/wordpress/86470/digital-id/protonmail-accused-surveillance.html
Durov accused the Russian authorities of trying to hack Telegram accounts of Ural journalists

Friday night, unknown persons tried to hack Telegram and Facebook accounts of famous journalists in Yekaterinburg. The Deputy Editor-in-Chief "URA.RU" Anton Olshannikov, PR specialist Platon Mamatov and the Editor-in-Chief of the site "MSTROK" (mstrok.ru) Natalia Vakhonina suffered from the actions of the unknown hacker. In addition, unknown persons attempted to gain access to the telegram channel of the portal "Momenty" (https://tlg.name/s/momenty_ekb/3292). It is interesting to note that all of them actively wrote about the protests against the construction of the temple in Yekaterinburg.
https://www.ehackingnews.com/2019/05/durov-accused-russian-authorities-of.html
Never heard of TrueCaller? They might have heard about you. Here is how you can unlist yourself
Could an app you have never even heard of put you at risk? This is what happened to Chloe (real name has been changed), an investigative journalist exposed by an app that her source was using.
Her source was using TrueCaller, an app that aims to identify phone numbers so users can filter out calls, even if it is from a number they have never encountered before. TrueCaller relies on users tagging numbers who are calling them. And when your number is tagged there is no way for you to know that you are in TrueCaller’s database.
Chloe’s story, which we are publishing today, is evidence of the concrete threat that TrueCaller can be to those working in a hostile environment.
Technology
Restoring the original gameboy - Retroration project
In this week’s project I will restore the original Nintendo Gameboy. As a 90’s kid I thought it would be cool to restore a Gameboy. Or should I say retrore. I bought this one from Japan. It’s obviously dirty but it’s also very yellow no rust this time. With this rust would be very bad. However the screen is broken and it is missing a lot of vertical lines. Otherwise it seems to be fine. I had some issues with turning it on when I tested it but after I got it on, I’ve had no trouble. The batteries I used were probably dead. It’s also missing the screen cover/lens. I bought a new one
Science
New Causes of Autism Found in ‘Junk’ DNA

Leveraging artificial intelligence techniques, researchers have demonstrated that mutations in so-called ‘junk’ DNA can cause autism. The study, published May 27 inNature Genetics, is the first to functionally link such mutations to the neurodevelopmental condition.
The research was led by Olga Troyanskaya in collaboration with Robert Darnell. Troyanskaya is deputy director for genomics at the Flatiron Institute’s Center for Computational Biology (CCB) in New York City and a professor of computer science at Princeton University. Darnell is the Robert and Harriet Heilbrunn Professor of Cancer Biology at Rockefeller University and an investigator at the Howard Hughes Medical Institute.https://www.simonsfoundation.org/2019/05/27/autism-noncoding-mutations/
Sonic black holes produce “Hawking radiation,” may confirm famous theory

Israeli physicists think they have confirmed one of the late Stephen Hawking's most famous predictions by creating the sonic equivalent of a black hole out of an exotic superfluid of ultra-cold atoms. Jeff Steinhauer and colleagues at the Israel Institute of Technology (Technion) described these intriguing experimental results in a new paper in Nature.
The standard description of a black hole is an object with such a strong gravitational force that light can't even escape once it moves behind a point of no return known as the event horizon. But in the 1970s, Hawking demonstrated that—theoretically, at least—black holes should emit tiny amounts of radiation and gradually evaporate over time.
Blame the intricacies of quantum mechanics for this Hawking radiation. From a quantum perspective, the vacuum of space continually produces pairs of virtual particles (matter and antimatter) that pop into existence and just as quickly annihilate away. Hawking proposed that a virtual particle pair, if it popped up at the event horizon of a black hole, might have different fates: one might fall in, but the other could escape, making it seem as if the black hole were emitting radiation. The black hole would lose a bit of its mass in the process. The bigger the black hole, the longer it takes to evaporate.
SciFi
Amazon’s Good Omens is very bit as entertaining as original novel

Heaven and Hell prepare to face off in the long-planned battle of Armageddon, but an angel, a demon, and a rebellious Antichrist aren't quite as enthusiastic about the prospect in Good Omens. The six-part limited series is based on the original 1990 novel by Neil Gaiman and the late Terry Pratchett, and it's every bit as entertaining as the source material.