My Weekly RoundUp #97
This week I want to launch a new section in my Weekly Roundup: "INBOX" will contain my answers to questions and suggestions from readers, which I receive frequently, also via email and social media.
INBOX
A new incident response tool by Veeral Patel

Veeral wrote me about his IR tool, called "Incidents":
I've been building this open source project for investigating large security incidents:
https://github.com/veeral-patel/incidents
http://veeral-patel.com/incidentsI'd like to find a few DFIR professionals to start using it, to get feedback. Is there anyone you know who'd find it useful?
In my opinion, I find it an interesting project: the tree structure of the tickets provides to the incident manager an extremely clear view.
I'll probably try to organize a trial in my IR team: if you do the same, send your feedbacks to Veeral!
Android forensics tools request

Henrx Badr asks:
Im looking for a distro or some tools that will help remove FRP/Unlock Carrier/Flash Partitions on Android phones… any help will be excellent!
A useful distro for Android Forensics is Santoku Linux: it contains all required tools to perform required operations. Another great tool is Andriller: it permits almost all kinds of data extraction from Android devices.
Procedures for unlocking/reflash and FRP removal may differs depending the device, so my suggestion is a search on XDA forum.
A suggestion for my TCPDUMP cheatsheet
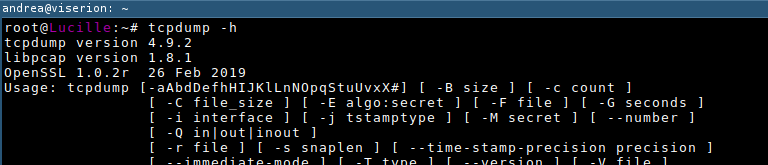
Regarding my TCPDUMP cheatsheet, SysAdmin suggests:
If you need to get rid of strings like
STP 802.1d, Config, Flags [none], bridge-id 8000.00:30:19:2c:93:41.8041, length 42
in the tcpdump’s output try adding “not ether host 01:00:0c:cc:cc:cd” filter (exact value can be found via -e flag).
Nice tip, dude! Many thanks!
Some troubles with iCat
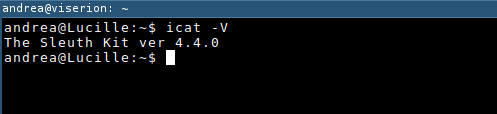
In the comments of post How to extract data and timeline from Master File Table on NTFS filesystem, JK reports:
Not sure if icat got updated or what, but it doesn’t the stdout argument.
The tutorial has developed using the last SleutKit version available on my Debian 9:
$ icat -V
The Sleuth Kit ver 4.4.0
The current version is the 4.6.6, so I've downloaded and compiled it in order to check: icat work well with stdout.
Can you send me more details and the output of your icat?
And now some interesting news!
Cybersecurity
Millions of Exim mail servers are exposed to attacks due to a critical vulnerability that makes it possible for unauthenticated remote attackers to execute arbitrary commands
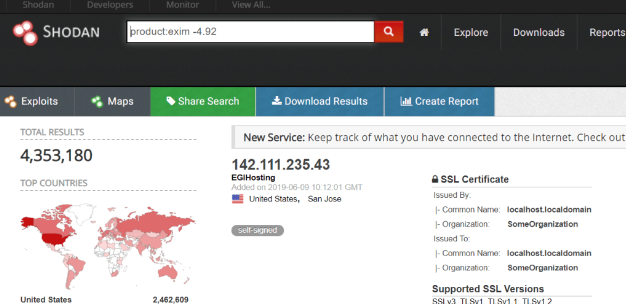
A critical vulnerability affects versions 4.87 to 4.91 of the Exim mail transfer agent (MTA) software. The flaw could be exploited by unauthenticated remote attackers to execute arbitrary commands on mail servers for some non-default server configurations.
The vulnerability, tracked as CVE-2019-10149, resides in the deliver_message() function in /src/deliver.c and it is caused by the improper validation of recipient addresses. The issue could lead to remote code execution with root privileges on the mail server.
“In this particular case, RCE means Remote Command Execution, not Remote Code Execution: an attacker can execute arbitrary commands with execv(), as root; no memory corruption or ROP (Return-Oriented Programming) is involved.” reads the security advisory published by Qualys. “This vulnerability is exploitable instantly by a local attacker (and by a remote attacker in certain non-default configurations).”
The CVE-2019-10149 flaw was called ‘The Return of the WIZard,” a reference to Sendmail’s ancient WIZ and DEBUG vulnerabilities.https://securityaffairs.co/wordpress/86864/hacking/exim-flaw-cve-2019-10149.html
Microsoft NTLM Flaws Expose All Windows Machines to RCE Attacks

Two critical vulnerabilities in Microsoft's NTLM authentication protocol consisting of three logical flaws make it possible for attackers to run remote code and authenticate on machines running any Windows version.
As Preempt's research team discovered, threat actors can "remotely execute malicious code on any Windows machine or authenticate to any web server that supports Windows Integrated Authentication (WIA) such as Exchange or ADFS."
The Windows NTLM (short for NT LAN Manager) Authentication Protocol is used for client/server authentication purposes to authenticate remote users and to provide session security when requested by application protocols.
Privacy
RAMBleed Attack Can Steal Sensitive Data From Computer Memory

Researchers found a new vulnerability that impacts the confidentiality of data stored in a computer's memory. Using it, they were successfully able to extract a signing key from an OpenSSH server using normal user privileges.
Dubbed RAMBleed, the attack is based on the Rowhammer vulnerability and can be used to break the safe-storage promise of random access memory (RAM) modules; even those that integrate error-correcting code (ECC) mechanism.
Rowhammer started as an experimental study that tested the isolation of information loaded in RAM. As memory modules became physically smaller and their storage larger, the space between the inner cells grew shorter; which created an opportunity for electrical interference that could change the charge of the memory bits.
Technology
The NYC subway system runs on OS/2, IBM’s old PC operating system
Despite the failure of OS/2 in the consumer market, it was hilariously robust, leading to a long life in industrial and enterprise systems—with one other famous example being ATMs. Waldhauer said, “Thinking about all the operating systems in use [in the MTA], I’d have to say that OS/2 is probably the most robust part of the system, except for the mainframe.” It’s still in use in the NYC subway system in 2019. IBM had long given up on it, even allowing another company to maintain the software in 2001.
Why SpaceX is Making Starlink
Programming
Visual Studio Code Remote Development over SSH to a Raspberry Pi is butter

There's been a lot of folks, myself included, who have tried to install VS Code on the Raspberry Pi. In fact, there's a lovely process for this now. However, we have to ask ourselves is a Raspberry Pi really powerful enough to be running a full development environment and the app being debugged? Perhaps, but maybe this is a job for remote debugging. That means installing Visual Studio Code locally on my Windows or Mac machine, then having Visual Studio code install its headless server component (for ARM7) on the Pi.
https://www.hanselman.com/blog/VisualStudioCodeRemoteDevelopmentOverSSHToARaspberryPiIsButter.aspx
Comparing the Same Project in Rust, Haskell, C++, Python, Scala and OCaml
During my final term at UWaterloo I took the CS444 compilers class with a project to write a compiler from a substantial subset of Java to x86, in teams of up to three people with a language of the group’s choice. This was a rare opportunity to compare implementations of large programs that all did the same thing, written by friends I knew were highly competent, and have a fairly pure opportunity to see what difference design and language choices could make. I gained a lot of useful insights from this. It’s rare to encounter such a controlled comparison of languages, it’s not perfect but it’s much better than most anecdotes people use as the basis for their opinions on programming languages.
http://thume.ca/2019/04/29/comparing-compilers-in-rust-haskell-c-and-python/
Music
Radiohead releases online ‘OK Computer’ sessions that thief tried to ransom
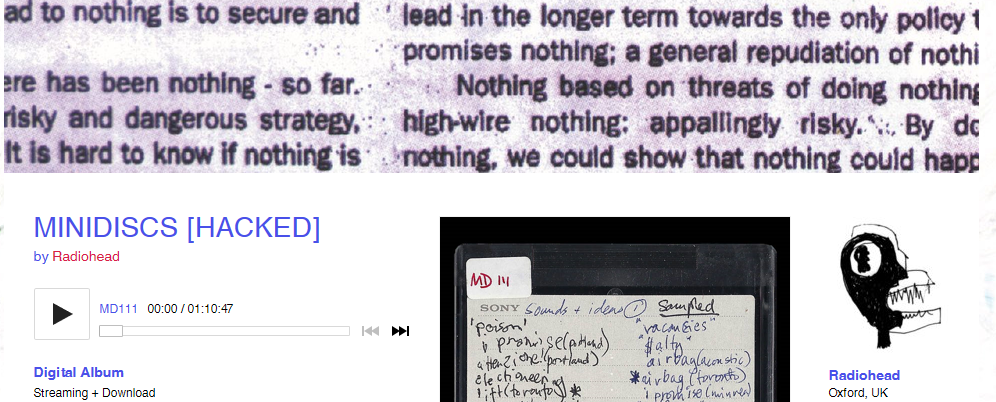
Well, bless your heart, the band Radiohead said after it was hacked and asked to pay a ransom for 18 hours of unheard music – a request that it eschewed, instead releasing the music on Bandcamp in order to aid Extinction Rebellion.
Want it? Here you go. It will cost you an £18 (around $23) donation to aid the climate advocacy group.
The extortionist demanded $150,000 after stealing 18 hours of music last week, according to a tweet from Radiohead guitarist Jonny Greenwood on Tuesday. It was stolen from Radiohead frontman Thom Yorke’s archive from around the time of the release of the 1997 album OK Computer.https://radiohead.bandcamp.com/
https://nakedsecurity.sophos.com/2019/06/12/radiohead-releases-ok-computer-sessions-that-hacker-tried-to-ransom/
