CVE-2019-15846 - Seriously? Another RCE in Exim?
Ok, it is true that Exim is one of the most used SMTP servers in the world, and for this reason it is continuously monitored by many security experts, but in the last months the Remote Code Execution vulnerabilities found are a lot!
The vulnerability
In an advisory released by Tenable last friday, the researcher Ryan Seguin says that
an unauthenticated remote attacker could send a malicious SNI ending in a backslash-null sequence during the initial TLS handshake, which causes a buffer overflow in the SMTP delivery process. This would allow an attacker to inject malicious code that Exim then arbitrarily executes as root. This vulnerability does not depend on the TLS library in use, so both GnuTLS and OpenSSL are affected.
The default Exim configuration file does not have TLS enabled, but most organizations are required to enable it for standard internet traffic handling purposes. Some versions of Exim bundled with operating systems may have TLS enabled by default.
The Exim team has released version 4.92.2 to fix this vulnerability, and administrators are encouraged to upgrade as soon as possible. While the official security advisory notes that disabling TLS does mitigate the vulnerability, it is strongly recommended not to do so.
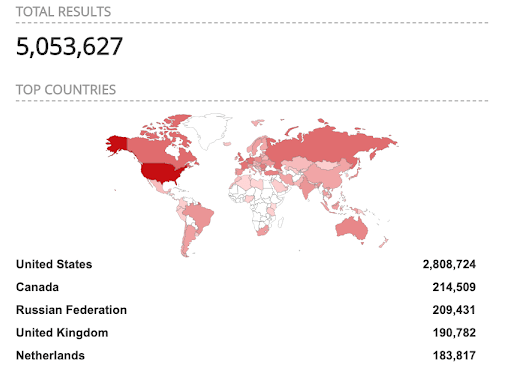
A massive attack surface
According to Shodan, over 5 million of Exim hosts are internet-facing, so the attack surface for the flaw is massive.
While no public exploit of the vulnerabilities have yet been reported, according to the Exim team, a rudimentary proof-of-concept (PoC) does exist (but has not been made public).
Update, update ASAP!
- https://nvd.nist.gov/vuln/detail/CVE-2019-15846
- https://www.tenable.com/blog/cve-2019-15846-unauthenticated-remote-command-execution-flaw-disclosed-for-exim
- http://exim.org/static/doc/security/CVE-2019-15846.txt
- https://www.andreafortuna.org/2017/11/28/cve-2017-16943-exim-remote-code-execution-vulnerability/
- https://www.andreafortuna.org/2018/03/07/cve-2018-6789-oops-another-rce-vulnerability-on-exim/