Cybersecurity Roundup #20
A lot of vulnerabilities, some cybercrime stuff and a serious privacy concern on Xiaomi phones.
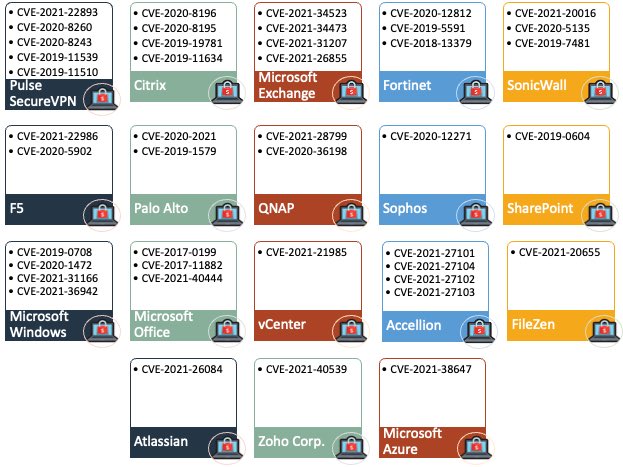
A group of researchers compiled a list of the main CVE exploited by ransomware groups
Several security researchers around the world are compiling a list containing all the vulnerabilities that ransomware groups and their affiliates are using as initial access to their victims' networks.
The operation started on Twitter, following the proposal made by Allan Liska, a member of the CSIRT of Recorded Future: in a few days, the list grew rapidly to include security flaws found in the products of over a dozen different software and hardware providers, and expanded to include actively exploited defects.
Among the vulnerabilities listed, the recent problems of the MSHTL engine (CVE-2021-40444), the ProxyShell vulnerability (CVE-2021-34473, CVE-2021-34523, CVE-2021-31207), the attack technique PetitPotam (CVE-2021-36942) and the PrintNightmare vulnerability (CVE-2021-34527).
Europol's Blitz against an online organization led to 106 arrests
Law enforcement agencies in Italy and Spain dismantled a criminal organization involved in online fraud, money laundering, drug trafficking and property crimes, which have yielded criminals about 10 million euros of illegal proceeds in a year. "Criminals have defrauded hundreds of victims through phishing attacks and other types of online fraud such as SIM swaps and business email compromise before recycling money through an extensive network of contacts and comfortable companies", Europol said in a statement.
The group operated in Tenerife, in the Spanish Canary Islands. The development comes as a result of a year-long operation that saw 106 arrests and seizures of electronic devices, credit cards, SIM cards, POS terminals, a marijuana plantation and the equipment used for its cultivation and distribution. Illicitly acquired profits were then recycled through an extensive network of money laundry and convenience companies. The investigation was undertaken jointly by the Spanish National Police (Policía Nacional) and supported by the Italian National Police (State Police), Europol and Eurojust.
Details of a new vulnerability detected in Apple MacOS have been announced
Researchers at the security firm SSD Security have disclosed details of a new vulnerability in Apple's MacOS Finder, which allows malicious users to execute arbitrary commands on Mac running any version of macOS until the latest version, Big Sur.
The security issue is caused by the way macOS processes '.inetloc' files, system-wide bookmarks that can be used to open online resources (news://, ftp://, afp://) or local files (file://), which inadvertently makes him execute any command embedded by an attacker inside without any warning or prompt.
According to the report, "these files can be embedded in emails that if the user clicks on them will execute the built-in commands within them without providing a prompt or warning to the user."
Apple solved the problem with the latest MacOS update, without assigning a CVE identification number: however, according to the researchers, the Apple patch would only partially resolve the defect as it can still be exploited by changing the protocol used to run the built-in commands from 'file://' to 'FiLe://'.
The Lithuanian government warns about the features of secret censorship in Xiaomi devices
The Lithuanian Ministry of Defense has published a security audit for three popular 5G smartphone models manufactured in China, recommending citizens avoid or stop using at least two of the three devices, citing privacy violations and undocumented censorship features.
The 5G smartphone models selected for the audit included the OnePlus 8T 5G, the Huawei P40 5G and the Xiaomi Mi 10T 5G.
According to Margiris Abukevičius, Deputy Minister of National Defense, the phones were selected because they had previously been identified by the international community as "devices that present some cybersecurity risks". The government audit, available on ministry's website, did not find any problems with OnePlus 8T 5G, but noted some critical issues in the other two models. Most of the issues were detected in the Xiaomi Mi 10T, where officials said they discovered a secret censorship module that can detect and block 449 keywords or keyword groups in Chinese and Latin characters related to sensitive topics within China, such as "Free Tibet", "Voice of America", "Democratic Movement", "Taiwan's Independence Wish" and others.
According to the audit, the module was disabled in the devides distributed in Lithuania and the EU region, but they also found a function that could have allowed Xiaomi to silently enable it without the user's knowledge.
A design problem in the Microsoft Exchange autodiscover service could lead to exposure of domain credentials
Researchers at the security company Guardicore discovered and disclosed details of a design flaw in a Microsoft Exchange email server feature that can be abused to collect the credentials of the domain hosting it.
Discovered by the researcher Amit Serper, the bug lies in the Microsoft Autodiscover protocol, an Exchange email server feature that allows clients to automatically discover email servers, provide credentials and then receive appropriate configurations: the protocol is a crucial part of Exchange email servers as it allows administrators an easy way to make sure clients use SMTP, IMAP, LDAP, WebDAV and other appropriate settings.
However, to obtain these automatic configurations, mail clients typically attempt to access a series of predetermined URLs derived from the domain of the user's email address (e.g. https://autodiscover.example.com/autodiscover/autodiscover.xml or http://autodiscover.example.com/autodiscover/).
Guardicore researchers registered the domain name "autodiscover" on all major TLDs still available, using them as honeypot to estimate the extent of the problem. It turned out that for more than four months, between April 16, 2021 and August 25, 2021, these servers received hundreds of requests, complete with thousands of credentials, from users who were trying to configure their email clients.
In the report Serper provides some mitigations that administrators can apply to prevent this loss of data (such as blocking all autodiscover.[tld] domains and disabling Basic authentication), although in his opinion it would also need an update by Microsoft to the design of the automatic detection protocol.
REvil ransomware operators hijack ransom negotiations by excluding affiliates
According to BleepingComputer, REvil operators are hijacking ransom negotiations, excluding their affiliates from the agreement to obtain the full amount.
The REvil ransomware, also known as Sodinokibi, emerged in the first half of 2019 and is a successor to the GandCrab ransomware-as-a-service (RaaS). The RaaS business model involves a developer who creates ransomware and configures the infrastructure, and affiliates recruited to violate and encrypt victim data. Compensation is divided between the two parties with affiliates taking the largest denomination (usually 70-80%). According to Advanced Intel researchers, at least since 2020 various actors on underground forums have said that REvil operators were dealing with victims in secret chats obtaining the full ransom, without the knowledge of affiliates.
A researcher on an underground forum provided evidence of REvil's double-dipping practices, talking about a "cryptobackdoor" in REvil samples: affiliates were not the only ones able to decipher the affected systems but REvil operators also had a main key that they could use to restore files.
That key recovered from a sample of the ransomware was used by Bitdefender for its decryption tool that probably helped Kaseya's victims recover files for free. According to the analyses, samples analyzed after the group restarted the operations no longer had this additional key.
After rebranding as BlackMatter, the group was opened up on this practice, letting everyone know that they reserved the right to take over the negotiations at any time, without giving explanation.