Forensic Artifacts: evidences of program execution on Windows systems
During a forensic analysis of a Windows system, it is often critical to understand when and how a particular process has been started.
In order to identify this activity, we can extract from the target system a set of artifacts useful to collect evidences of program execution.
UserAssist
On a Windows System, every GUI-based programs launched from the desktop are tracked in this registry key:
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{GUID}\Count
This key contains two GUID subkeys (CEBFF5CD Executable File Execution, F4E57C4B Shortcut File Execution): each subkey maintains a list of system objects such as program, shortcut, and control panel applets that a user has accessed.
Registry values under these subkeys are weakly encrypted using ROT-13 algorithm which basically substitutes a character with another character 13 position away from it in the ASCII table.
All values are ROT-13 Encoded, some tips:
.exe = .RKR
.lnk = .YAX
Background Activity Moderator (BAM)
BAM is a Windows service that Controls activity of background applications.
This service exists in Windows 10 only after Fall Creators update - version 1709.
It provides full path of the executable file that was run on the system and last execution date/time, and its located in this registry path:
HKLM\SYSTEM\CurrentControlSet\Services\bam\UserSettings\{SID}
It contains a list of paths and executables, and the value of each of those is the time last executed in Filetime (64bit little Endian) format in UTC:
RecentApps
Program execution launched on a Win10 system is tracked in the RecentApps key:
HKCU\Software\Microsoft\Windows\Current Version\Search\RecentApps
Each GUID key points to a recent application:
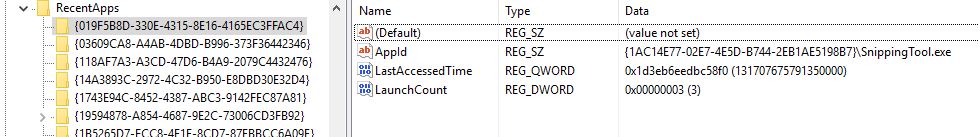
AppID = Name of Application
LastAccessTime = Last execution time in UTC
LaunchCount = Number of times executed
ShimCache
Windows Application Compatibility Database is used by Windows to identify possible application compatibility challenges with executables, and it tracks the executables’ file name, file size, last modified time.
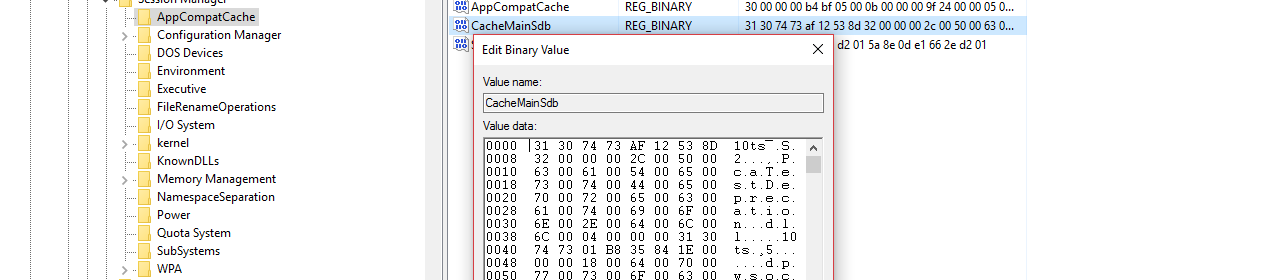
Last 1024 programs executed on the Windows system could be found in this key :
HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\AppCompatCache
You can use this key to identify systems that specific malware was executed on, using a specific tool like ShimCacheParser.py, by Mandiant (https://github.com/mandiant/ShimCacheParser)
Notes
- On Windows 7/8/10 contains at most 1,024 entries
- LastUpdateTime does not exist on Win7/8/10 systems
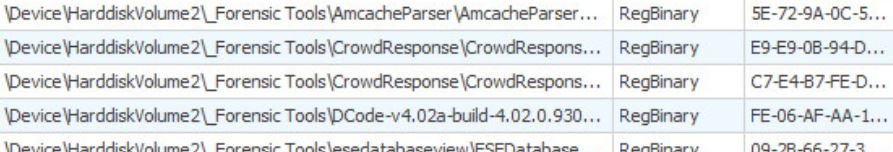
Amcache
ProgramDataUpdater (a task associated with the Application Experience Service) uses the registry file Amcache.hve to store data during process creation, located in
C:\Windows\AppCompat\Programs\Amcache.hve
This registry stores the first execution of a program on the system, including portable programs executed from an external storage.
The file can be analyzed using the amcache plugin of RegRipper (https://github.com/keydet89/RegRipper2.8)
For more information about Amcache and Shimcache in forensic analysis, please refer to this specific article: Amcache and Shimcache in forensic analysis
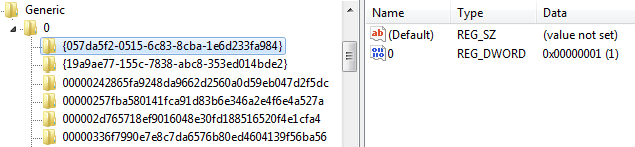
Jump Lists
The Windows 7-10 task bar (Jump List) is engineered to allow users to “jump” or access items they have frequently or recently used quickly and easily.
This functionality cannot only include recent media files; it must also include recent tasks.
The data stored in the folder
%USERPROFILE%\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations
will each have a unique file prepended with the AppID of the associated application.
The AutomaticDestinations Jump List files are OLE Compound Files containing multiple streams of which:
- hexadecimal numbered, e.g. "1a"
- DestList
Each of the hexadecimal numbered streams contains data similar of that of a Windows Shortcut: data can be extracted and analyzed with a LNK parser, such as lnk-parse (https://github.com/lcorbasson/lnk-parse).
Prefetch
Windows Prefetch files, are designed to speed up the application startup process. The Prefetch files are stored into the path
%windir%\Prefetch
and contains the name of the executable, a Unicode list of DLLs used by that executable, a count of how many times the executable has been run, and a timestamp indicating the last time the program was run.
In this folder are stored information for the last 128 executables on Win7, and last 1024 on Win8-10.
Prefetch file can be parsed and analyzed using tools like PeCMD (https://github.com/EricZimmerman/PECmd)