My Weekly RoundUp #83
Last week I had a lot of work, so I fell behind with my usual readings.
Here some highlights (less is more, right?)
Cybersecurity
Windows Exploit Suggester - Next Generation (WES-NG)
WES-NG is a tool which based on the output of Windows'
systeminfoutility provides you with the list of vulnerabilities the OS is vulnerable to, including any exploits for these vulnerabilities. Every Windows OS between Windows XP and Windows 10, including their Windows Server counterparts, is supported.
NSA Software Reverse Engineering Framework: Ghidra

Ghidra is a software reverse engineering (SRE) framework created and maintained by the National Security Agency Research Directorate. This framework includes a suite of full-featured, high-end software analysis tools that enable users to analyze compiled code on a variety of platforms including Windows, Mac OS, and Linux. Capabilities include disassembly, assembly, decompilation, graphing, and scripting, along with hundreds of other features. Ghidra supports a wide variety of process instruction sets and executable formats and can be run in both user-interactive and automated modes. Users may also develop their own Ghidra plug-in components and/or scripts using Java or Python.
Google Discloses Unpatched 'High-Severity' Flaw in Apple macOS Kernel

Discovered by Project Zero researcher Jann Horn and demonstrated by Ian Beer, the vulnerability resides in the way macOS XNU kernel allows an attacker to manipulate filesystem images without informing the operating system.
The flaw could eventually allow an attacker or a malicious program to bypass the copy-on-write (COW) functionality to cause unexpected changes in the memory shared between processes, leading to memory corruption attacks.
https://bugs.chromium.org/p/project-zero/issues/detail?id=1726&q=
Programming
calc.exe is now open source
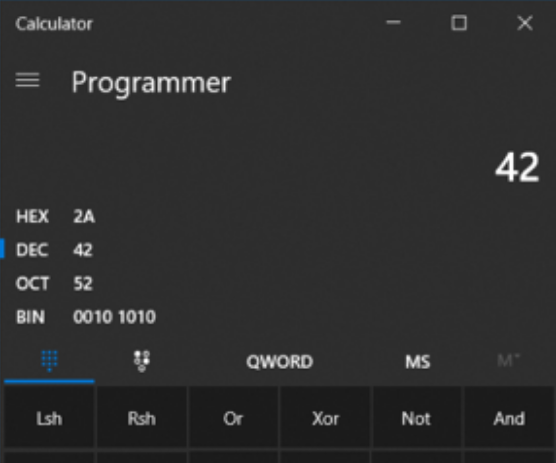
Microsoft's embrace and adoption of open source software has continued with the surprising decision to publish the code for Windows Calculator and release it on GitHub under the permissive MIT license.
The repository shows Calculator's surprisingly long history. Although it is in some regards one of the most modern Windows applications—it's an early adopter of Fluent Design and has been used to showcase a number of design elements—core parts of the codebase date all the way back to 1995.
Privacy
Guess what? Facebook still tracks you on Android apps (even if you don't have a Facebook account)
In December 2018, we revealed how some of the most widely used apps in the Google Play Store automatically send personal data to Facebook the moment they are launched. That happens even if you don't have a Facebook account or are logged out of the Facebook platform (watch our talk at the Chaos Communication Congress (CCC) in Leipzig or read our full legal analysis here).
Today, we have some good news for you: we retested all the apps from our report and it seems as if we have made some impact. Two thirds of all apps we retested, including Spotify, Skyscanner and KAYAK, have updated their apps so that they no longer contact Facebook when you open the app.
Here’s the bad news: seven apps, including Yelp, the language-learning app Duolingo and the job search app Indeed, as well as the King James Bible app and two Muslim prayer apps, Qibla Connect and Muslim Pro, still send your personal data to Facebook before you can decide whether you want to consent or not. Keep in mind: these are apps with millions of installs.
Since we published our report, mobilsicher.de could also confirm that apps on iOS exhibit similar behaviour.
Facebook Messenger Bug Exposed Who You Were Chatting With to Hackers
Cybersecurity software company Imperva—which previously identified another bug that allowed websites to see Facebook users’ “likes,” location history, and interests—shared its report on the vulnerability in a blog post by researcher Ron Masas on Thursday. With this bug, hackers could potentially use someone’s browser to exploit iframe properties to see who they’d been chatting with on Messenger.