My Weekly RoundUp #89
Bendgate 2.0, Sea Turtle Hijacking and some problems for 'Wannacry Hero'
Privacy
The mystery of the Amazon Echo data

With over 6.3 million Amazon Echo devices worldwide, there is a good chance these constantly active devices will record criminal behavior.
Bloomberg, who recently reported on yet another creepy feature, that Amazon workers are listening to what you tell Alexa, were told by workers that audios shared on internal chat rooms include a child screaming for help and potential sexual assaults.
Smart speakers are constantly active. They listen in short snippets (a few seconds) in order to detect whether the ‘wake word’ has been used and then delete the information if the word is not detected. There are multiple stories about devices wrongly detecting the wake word, recording unexpectedly, speaking when a wake word has not been used, and even sending audios to strangers.https://privacyinternational.org/blog/2819/mystery-amazon-echo-data
How Google Builds a Profile on Everyone
There’s a lot of talk about the invasive practices of FaceBook right now, but somehow Google has skated by largely unfazed by the public outcry against privacy violations and the snowballing impact of too much personal information being out there with ambiguous consent from the parties being snooped on.
Through the lens of privacy activism, this is interesting, because FaceBook is in many ways less bad than Google. For a lot (but not all) of FaceBook services, you have to have an account or install their apps in order to give up your data. People who refuse to participate are still tracked by FaceBook cookies and url tracking.
The difference is that Google’s method of attack is by aggregation. Google builds many tools that are useful to users and administrators, but they are engineered to gather data about users and build as much of a profile as possible, which is then sold to advertisers, governments, other data brokers, or anyone else who is willing to pay.
Technology
My Samsung Galaxy Fold screen broke after just a day
Look closely at the picture above, and you can see a small bulge right on the crease of my Galaxy Fold review unit. It’s just enough to slightly distort the screen, and I can feel it under my finger. There’s something pressing up against the screen at the hinge, right there in the crease. My best guess is that it’s a piece of debris, something harder than lint for sure. It’s possible that it’s something else, though, like the hinge itself on a defective unit pressing up on the screen.
It’s a distressing thing to discover just two days after receiving my review unit. More distressing is that the bulge eventually pressed sharply enough into the screen to break it. You can see the telltale lines of a broken OLED converging on the spot where the bulge is.
Bendgate 2.0: Samsung’s $2,000 foldable phone is already breaking

Samsung's futuristic Galaxy Fold is launching this month, and the device has already made its way to a select group of reviewers and influencers. During the run-up to the device's launch, there were concerns about the durability of the folding display, and now after just a few days with the public, the device is already experiencing problems. There are numerous reports of Samsung's $2,000 device breaking after a single day, sometimes due to poor durability, other times due to user error.
Samsung responds to Galaxy Fold screen damage: ‘we will thoroughly inspect these units’
Samsung has released an official statement addressing reports of display issues with the upcoming Galaxy Fold. There are two parts to the story, and unfortunately only one of those parts offers real answers.
First, Samsung notes that it intends to “thoroughly inspect [the review] units in person,” referring to the devices that seemed to have had screens break without a direct, obvious cause. Our review unit developed a bulge that appeared to be the result of something in between the screen and the hinge, ultimately breaking the screen. So we don’t have a clear answer there yet.
Separately, Samsung addressed the issue of screens breaking because reviewers had attempted to peel off a protective plastic layer that was adhered to the screen itself.
Cybersecurity
Marcus Hutchins pleads guilty to two counts of banking malware creation

The popular British cybersecurity expert Marcus Hutchins has pleaded guilty to developing and sharing the Kronos banking malware
between July 2014 and July 2015.
Marcus Hutchins, also known as MalwareTech, made the headlines after discovering the “kill switch” that halted the outbreak of the WannaCry ransomware
. In August 2017, he was arrested in Las Vegas after attending the Def Con hacking conference and was detained by the FBI in the state of Nevada.
In August 2017, Marcus Hutchins pleaded not guilty to charges of creating and selling malware at a hearing in Milwaukee, Wisconsin.
The court decided to relax the expert bail terms, allowing him to access the Internet and continues his ordinary working activities. The only restriction on Hutchins is that the expert cannot visit the Wannacry server domain.
The decision is unusual because computer crime suspects are not allowed to stay online.https://securityaffairs.co/wordpress/84260/cyber-crime/marcus-hutchins-pleads-guilty.htm
Amongst the WannaCry panic, a youngster in the UK calmly analysed the behaviour of the virus and quickly spotted what’s known as a “kill switch” in its programming.
If the ransomware was able to connect to a specific, weirdly named server, it would let you off and not scramble your files.
But if the call-home failed then the ransomware attack went ahead and you ended up facing a $300 extortion fee to get your files back.
For reasons we shall probably never know, the crooks who wrote WannaCry didn’t bother to purchase the domain name used by this safety valve, so our hero quietly registered the domain himself.
Then he set up a webserver that turned the safety valve on, so that pretty much everyone in the world with half-decent internet connectivity was automatically shielded from the data-zapping payload of the WannaCry attack.
This prompt and decisive action almost certainly saved many innocent users from those pay-$300-in-Bitcoin-right-now demands and prevented plenty of global heartache.
State-Backed “Sea Turtle” Hacker Group Hijacking Government Website Domains For Entire Countries3State-Backed “Sea Turtle” Hacker Group Hijacking Government Website Domains For Entire Countries

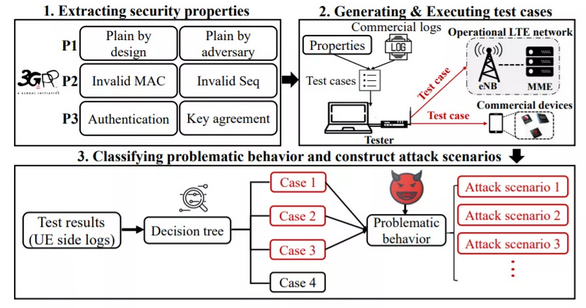
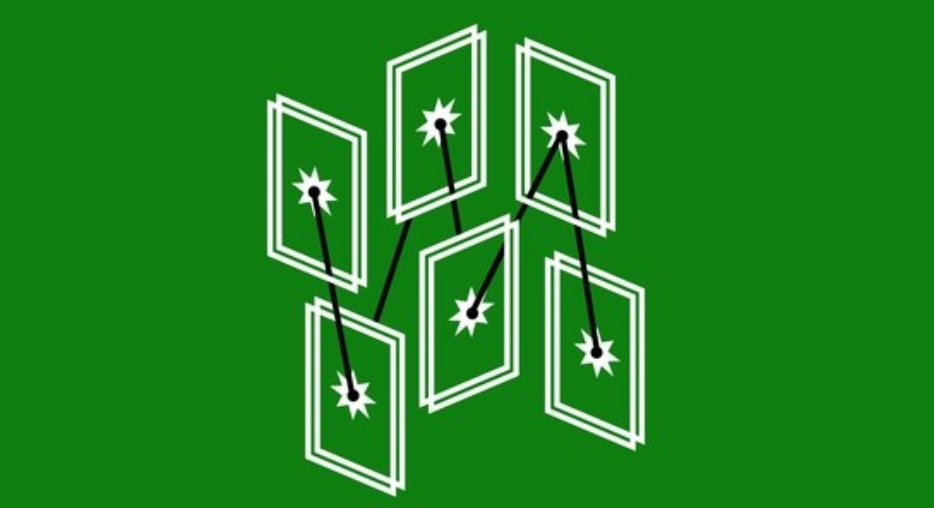
In brief, the hackers would change the target organization’s domain registration to point to their own DNS servers—the computers that perform the DNS translation of domains into IP addresses—instead of the victim’s legitimate ones. This sort of man-in-the-middle attack should be prevented by SSL certificates, but the hackers simply used spoofed certificates from Let’s Encrypt or Comodo, invalid on close inspection but still able to trick users with signs of legitimacy.
Cyberspies Hijacked the Internet Domains of Entire Countries
The wave of domain hijacking attacks besetting the Internet over the past few months is worse than previously thought, according to a new report that says state-sponsored actors have continued to brazenly target key infrastructure despite growing awareness of the operation.
The report was published Wednesday by Cisco’s Talos security group. It indicates that three weeks ago, the highjacking campaign targeted the domain of Sweden-based consulting firm Cafax. Cafax’s only listed consultant is Lars-Johan Liman, who is a senior systems specialist at Netnod, a Swedish DNS provider. Netnod is also the operator of
i.root, one of the Internet’s foundational 13 DNS root servers. Liman is listed as being responsible for the i-root. As KrebsOnSecurity reported previously, Netnod domains were hijacked in December and January in a campaign aimed at capturing credentials. The Cisco report assessed with high confidence that Cafax was targeted in an attempt to re-establish access to Netnod infrastructure.
The discovery of a new, sophisticated team of hackers spying on dozens of government targets is never good news. But one team of cyberspies has pulled off that scale of espionage with a rare and troubling trick, exploiting a weak link in the internet's cybersecurity that experts have warned about for years: DNS hijacking, a technique that meddles with the fundamental address book of the internet.
Researchers at Cisco's Talos security division on Wednesday revealed that a hacker group it's calling Sea Turtle carried out a broad campaign of espionage via DNS hijacking, hitting 40 different organizations. In the process, they went so far as to compromise multiple country-code top-level domains—the suffixes like .co.uk or .ru that end a foreign web address—putting all the traffic of every domain in multiple countries at risk.