My Weekly RoundUp #91
Strange weekend for Firefox users...
Technology
Firefox Addons Being Disabled Due to an Expired Certificate
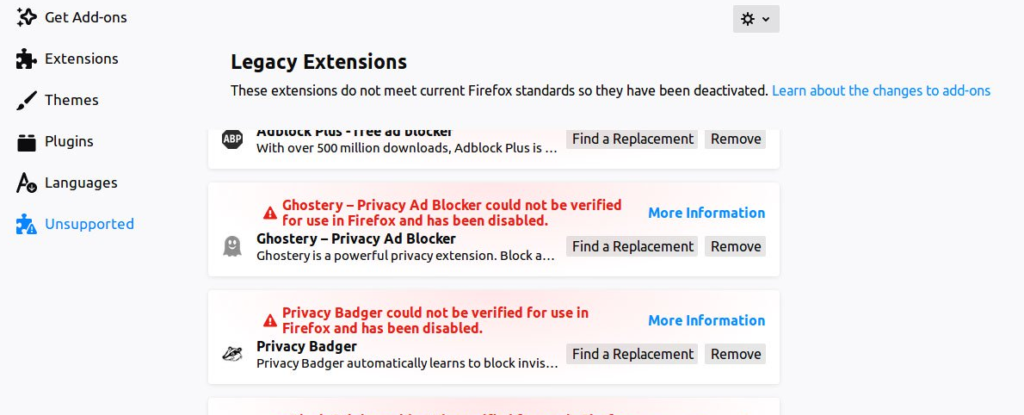
Mozilla Firefox users are discovering that all of their addons were suddenly disabled. It turns out that this is being caused by an expired intermediary certificate used to sign Mozilla addons.
In numerous reports on Reddit, Twitter, and bug reports on bugzilla, users were stating that their Mozilla addons were suddenly disabled with a message stating that they "could be verified for use in Firefox".
Many Firefox users around the world are browsing without their usual set of extensions after they suddenly stopped working earlier this evening. The event occurred as the clock rolled over on UTC (Coordinated Universal Time, aka GMT or Greenwich Mean Time), and impacted users quickly narrowed it down to "expiration of intermediate signing cert" -- as it's described on Mozilla's bug tracker.
Update 3 (5/4, 7:30 AM ET): The team has announced a hotfix is rolling out now. It's applied in the background, so you shouldn't have to do anything to receive it. However, to make sure you get it right away, you can follow these instructions
https://www.engadget.com/2019/05/03/firefox-extension-add-on-cert/?guccounter=1
Nightly, Dev and Android users may be able to disable signing of extensions; some users reported that this resolved the issue temporarily on their end. You need to set the preference xpinstall.signatures.required to false on about:config to disable signing. You could change the system date to the previous day to resolve it temporarily as well, but that can lead to other issues.
The issue can only be resolved on Mozilla's end. The organization needs to renew the certificate or create a new one to resolve the issue. I'd expect Mozilla to do that soon as the issue is widespread and affecting lots of Firefox users.
Users should not remove affected extensions from their installations; the issue will resolve itself once Mozilla fixes it.https://www.ghacks.net/2019/05/04/your-firefox-extensions-are-all-disabled-thats-a-bug/
Cybersecurity
Vodafone discovered backdoors in Huawei equipment. But it was 2011!

Vodafone, the largest mobile network operator in Europe, found backdoors in Huawei equipment between 2009 and 2011, reports Bloomberg. With these backdoors, Huawei could have gained unauthorized access to Vodafone's "fixed-line network in Italy." But Vodafone disagrees, saying that while it did discover some security vulnerabilities in Huawei equipment, these were fixed by Huawei and in any case were not remotely accessible, and hence they could not be used by Huawei.
Bloomberg's claims are based on Vodafone's internal security documentation and "people involved in the situation." Several different "backdoors" are described: unsecured telnet access to home routers, along with "backdoors" in optical service nodes (which connect last-mile distribution networks to optical backbone networks) and "broadband network gateways" (BNG) (which sit between broadband users and the backbone network, providing access control, authentication, and similar services).
In response to Bloomberg, Vodafone said that the router vulnerabilities were found and fixed in 2011 and the BNG flaws were found and fixed in 2012. While it has documentation about some optical service node vulnerabilities, Vodafone continued, it has no information about when they were fixed. Further, the network operator said that it has no evidence of issues outside Italy.
According to Bloomberg, Vodafone identified hidden backdoors in software that could have handed Huawei unauthorized access to the carrier’s fixed-line network in Italy used to connect to the internet.
“Now Vodafone Group Plc has acknowledged to Bloomberg that it found vulnerabilities going back years with equipment supplied by Shenzhen-based Huawei for the carrier’s Italian business.” reads the blog post published by Bloomberg. “While Vodafone says the issues were resolved, the revelation may further damage the reputation of a major symbol of China’s global technology prowess.”
Wait a moment … the flaws in the Huawei technology were discovered by Vodafone a decade ago
Bloomberg obtained Vodafone’s security briefing documents from 2009 and 2011 and spoke with people involved in the situation. The version provided by AFP, is slightly different because even if Vodafone confirmed the presence of the flaws, it is not true that bugs could have allowed unauthorized access to Italy’s fixed-line network.
https://securityaffairs.co/wordpress/84711/security/vodafone-huawei-backdoor.htmlh
Remote Code Execution on most Dell computers
What computer do you use? Who made it? Have you ever thought about what came with your computer? When we think of Remote Code Execution (RCE) vulnerabilities in mass, we might think of vulnerabilities in the operating system, but another attack vector to consider is “What third-party software came with my PC?”. In this article, I’ll be looking at a Remote Code Execution vulnerability I found in Dell SupportAssist, software meant to “proactively check the health of your system’s hardware and software” and which is “preinstalled on most of all new Dell devices”.
https://d4stiny.github.io/Remote-Code-Execution-on-most-Dell-computers/
As explained by Dell in its advisory, "An unauthenticated attacker, sharing the network access layer with the vulnerable system, can compromise the vulnerable system by tricking a victim user into downloading and executing arbitrary executables via SupportAssist client from attacker hosted sites."
The software flaw is tracked as CVE-2019-3719 and comes with a high severity CVSSv3 base score of 8.0 assigned by the National Vulnerability Database (NVD).
Dell patched the SupportAssist software during late April 2019 following an initial report received from 17-year old security researcher Bill Demirkapi on October 10, 2018.
Also, Dell advises all customers to update SupportAssist Client as soon as possible, seeing that all versions prior to 3.2.0.90 and later are vulnerable to remote code execution attacks
TinyPOS: a POS Malware written in Assembly
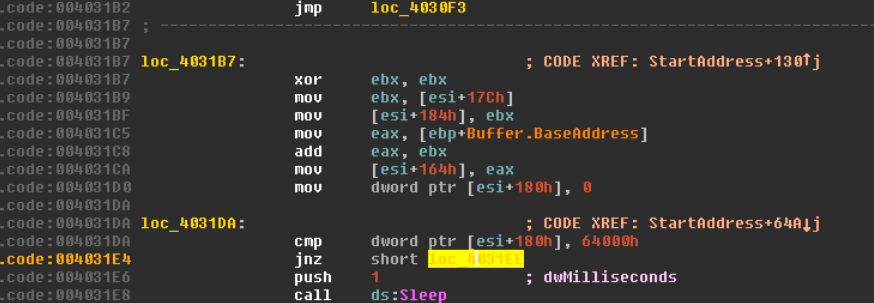
Legacy software vulnerabilities have created opportunities for hackers to steal credit card data and other personal information using tiny point of sale (POS) malware, according to research published by Forcepoint.
Researchers reportedly analyzed 2,000 samples of POS malware and found that many are handcrafted, written in assembly code and very small; thus, researchers aptly named the malware TinyPOS.
https://www.infosecurity-magazine.com/news/tinypos-handcrafted-malware-in-1
As we can see it doesn’t take hundreds or thousands of kilobytes of code to steal valuable credit card data ona largescale. The Tiny ecosystem is built from simpleyet effective components –each one being responsible for a dedicated task –written in a low-level programming language that only very few programmers (i.e. people working with embedded systems) consider their ‘weapon of choice’.While Swipe-and-Sign exists as an authentication option for card-present transactions, POS malware like TinyPOS will continue to be effective. We strongly recommend that retailers and banks aggressively pursue a faster move to EMV (at least Chip-and-Signature, preferably Chip-and-PIN).It is also recommended that an audit be performed on any system storing and transmitting personal data in relation to how that data is managed and stored. The goal should be to make it harder for credit card data to be extracted from the retailer’s systems. This includes while in transit.
https://www.forcepoint.com/sites/default/files/resources/files/report-tinypos-analysis-en.pdf
Privacy
Google now lets you auto-delete your app activity, location and web history
Google today announced that you can now auto-delete your location history and web and app activity by setting a time limit for how long Google can save this data.
Google will give you two options for this time limit: 3 or 18 months. Any data that is older than that will be automatically deleted. With this, you will still get recommendations, but the extent of your personal data that’s stored on Google’s servers and can be used by the company will be limited. The recommendations, too, will only be based on the limited recent data you still share, so they won’t be as precise as before, but should still be useful.

Whether you’re looking for the latest news or the quickest driving route, we aim to make our products helpful for everyone. And when you turn on settings like Location History or Web & App Activity, the data can make Google products more useful for you—like recommending a restaurant that you might enjoy, or helping you pick up where you left off on a previous search. We work to keep your data private and secure, and we’ve heard your feedback that we need to provide simpler ways for you to manage or delete it.
You can already use your Google Account to access simple on/off controls for Location History and Web & App Activity, and if you choose—to delete all or part of that data manually. In addition to these options, we’re announcing auto-delete controls that make it even easier to manage your data.
https://www.blog.google/technology/safety-security/automatically-delete-data/
Programming
Python at Netflix

As many of us prepare to go to PyCon, we wanted to share a sampling of how Python is used at Netflix. We use Python through the full content lifecycle, from deciding which content to fund all the way to operating the CDN that serves the final video to 148 million members. We use and contribute to many open-source Python packages, some of which are mentioned below. If any of this interests you, check out the jobs site or find us at PyCon. We have donated a few Netflix Originals posters to the PyLadies Auction and look forward to seeing you all there.
https://medium.com/netflix-techblog/python-at-netflix-bba45dae649e?source=rss----2615bd06b42e---4
The dark side of DevOps
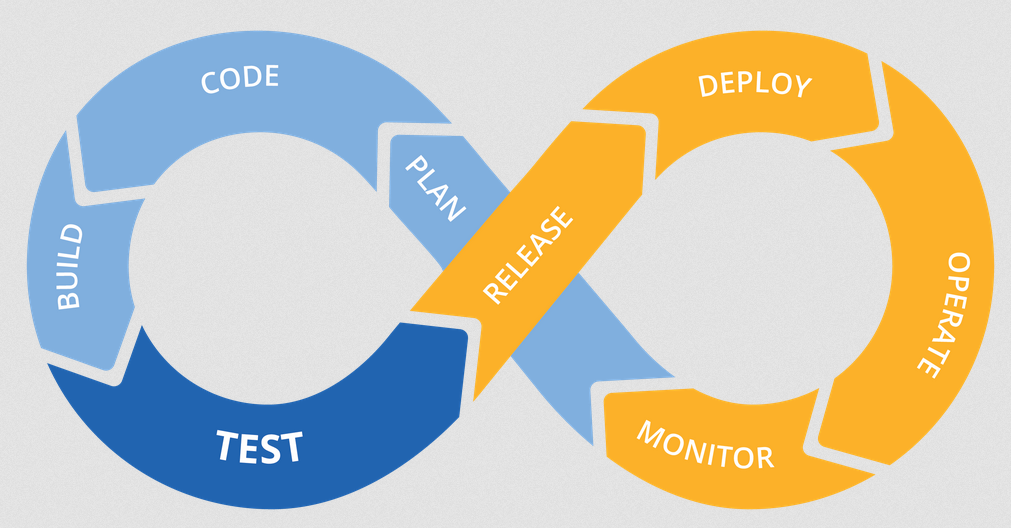
You’re already crafting your digital transformation strategy. Your organization is staffed with top-notch developers ready to implement the innovative, business-differentiating technologies you need to attract, engage, and retain customers. And you’ve invested in scaling Agile, driving DevOps adoption, automating the Continuous Delivery pipeline, and all the other components involved in moving from ideation to delivery as rapidly as possible. So what could possibly go wrong?
SciFi
Chewbacca actor Peter Mayhew is dead at 74
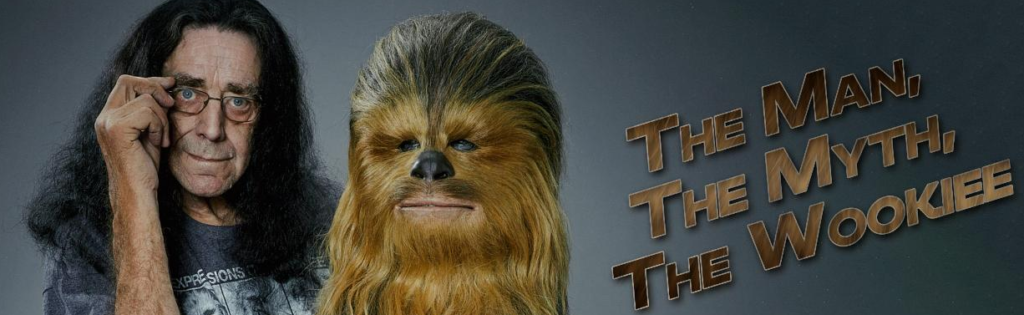
Peter Mayhew, who portrayed Chewbacca in all the character's live-action scenes until 2015's The Force Awakens, has died at his home in Texas. The British-born actor was 74 years old.
Mayhew was an aspiring actor working as a hospital orderly in 1976 when George Lucas tapped him to play the part. Mayhew's primary qualification for the job was his height: he stood 7 feet 3 inches tall (220 cm). That was tall enough to tower over Darth Vader, played by the six-foot-six (200 cm) David Prowse. Mayhew didn't utter Chewbacca's famous grunts and growls—those were voiced by sound-effects legend Ben Burtt.
According to The Hollywood Reporter, Mayhew went back to his hospital work after playing Chewie in Star Wars. He came back to play the character again in The Empire Strikes Back and then Return of the Jedi. By that point, his character had become famous enough that he could make his living on the convention circuit.https://arstechnica.com/gaming/2019/05/chewbacca-actor-peter-mayhew-is-dead-at-74/
What Avengers: Endgame did right and wrong

Avengers: Endgame debuted this weekend, breaking box-office records and speeding to a staggering $1.2 billion weekend take. It’s Marvel’s biggest movie ever, and at the current rate of ticket sales, it might just wind up as the biggest movie of all time. It’s hard to discuss Endgame as a single film, or even as the second half of the two-part story that started with Avengers: Infinity War, given how heavily it relies on the buildup of the other previous 20 films in Marvel Studios’ decade-plus of filmmaking. Forget smaller, more character-focused films like Spider-Man: Homecoming, Black Panther, or even Captain Marvel. Endgame is here to throw everything Marvel has at the audience, in one huge, spectacle-filled hurrah.
Naturally, there’s a lot to digest in this movie. So we sat down to discuss how Marvel got to this point, consider Endgame’s nagging issues, and figure out what the film’s ending means for Marvel’s future.
Avengers: Endgame Was Never Going to Have a Post-Credit Scene

The Marvel Cinematic Universe was built on mid- and post-credit scenes. That’s where some of the biggest, most shocking revelations came, linking what has become 22 movies and counting. And yet, fans who see the culmination of that story in Avengers: Endgame have been surprised to find out the credits this time serve the purpose of recognising the thousands of people who made the film, and nothing more. That’s what 11 years of conditioning will do.
Speaking to USA Today, the film’s directors Anthony and Joe Russo explained why they decided to break with MCU tradition and not add a scene during, or after, the credits.
“It was never in the cards,” Joe Russo said. “It was called ‘Endgame’ for a reason. This is it. This is the ending. The book is closed on that chapter of the Marvel universe and a new book will get written.”“This was the first Marvel movie we’ve done where we weren’t thinking about the future,” Anthony Russo added, referencing Captain America: The Winter Soldier, Captain America: Civil War, and Avengers: Infinity War, all of which they directed, and all of which had teases in the credits.
https://www.gizmodo.co.uk/2019/05/avengers-endgame-was-never-going-to-have-a-post-credit-scene/