‘Agent Smith’ malware has infected Android apps on 25 million devices
According to security firm Check Point, a newly discovered Android malware that replaces portions of apps with its own code has infected more than 25 million devices.
The malware doesn’t steal data from a user.
Instead, it hacks apps and forces them to display more ads or takes credit for the ads they already display so that the malware’s operator can profit off the fraudulent views.
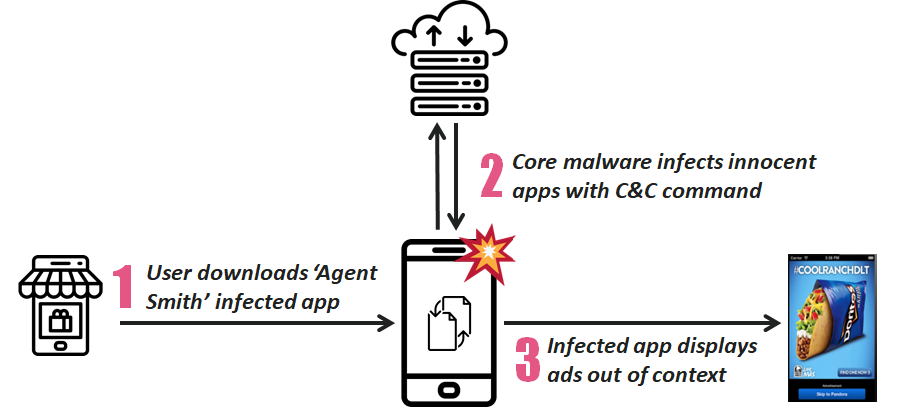
Dubbed Agent Smith, the malware takes advantage of multiple Android vulnerabilities, such as the Janus flaw and the Man-in-the-Disk flaw, and injects malicious code into the APK files of targeted apps installed on a compromised device and then automatically re-install/updates them without the victims' knowledge or interaction.
https://thehackernews.com/2019/07/whatsapp-android-malware.html
Check Point says the malware looks for known apps on a device, such as WhatsApp, Opera Mini, Swiftkey, TrueCaller, then replaces portions of their code and prevents them from being updated:
Disguised as Google related app, the core part of malware exploits various known Android vulnerabilities and automatically replaces installed apps on the device with malicious versions without the user’s interaction. This unique on-device, just-in-time (JIT) approach inspired researchers to dub this malware as “Agent Smith”.
“Agent Smith” currently uses its broad access to the device’s resources to show fraudulent ads for financial gain. This activity resembles previous campaigns such as Gooligan, HummingBad and CopyCat. The primary targets, so far, are based in India though other Asian countries such as Pakistan and Bangladesh are also affected.In a much-improved Android security environment, the actors behind Agent Smith seem to have moved into the more complex world of constantly searching for new loopholes, such as Janus, Bundle and Man-in-the-Disk, to achieve a 3-stage infection chain, in order to build a botnet of controlled devices to earn profit for the perpetrator. “Agent Smith” is possibly the first campaign seen that ingrates and weaponized all these loopholes and are described in detail below.
In this case, “Agent Smith” is being used to for financial gain through the use of malicious advertisements. However, it could easily be used for far more intrusive and harmful purposes such as banking credential theft. Indeed, due to its ability to hide it’s icon from the launcher and impersonates any popular existing apps on a device, there are endless possibilities for this sort of malware to harm a user’s device.
- https://research.checkpoint.com/agent-smith-a-new-species-of-mobile-malware/
- https://www.checkpoint.com/press/2019/25-million-infected-devices-check-point-research-discovers-new-variant-of-mobile-malware/#