Media File Jacking: WhatsApp and Telegram media files can be manipulated from attackers
According to a research published by Symantec, on Android systems attackers can manipulate media files transferred by users through the WhatsApp and Telegram messaging applications due to the way the Android operating system allows apps to access files in external storage.
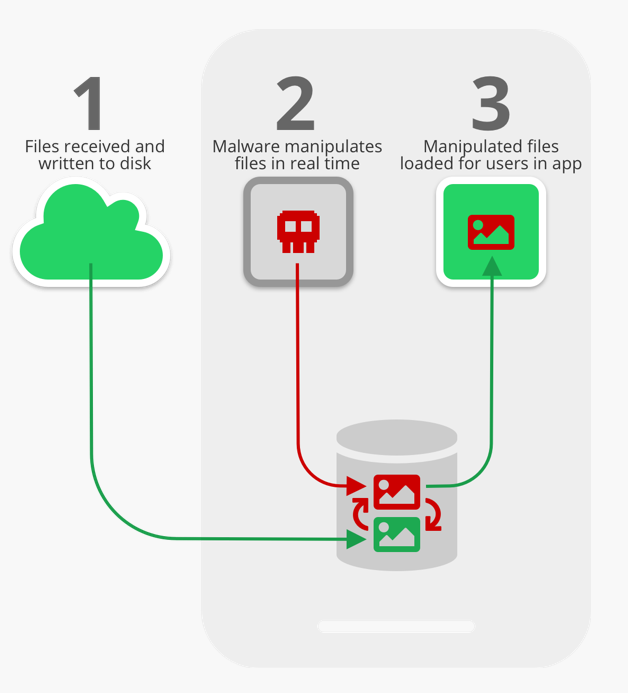
The attack method, dubbed “Media File Jacking” allows a malicious Android application with write-to-external storage permissions to quickly modify files sent or received via WhatsApp (in its default configuration) and Telegram (if the user has enabled the “Save to gallery” option) between the time they are written to the disk and the moment they are loaded in the app’s user interface.
Android apps can store files and data in two storage locations: internal and external storage. Files saved to internal storage are accessible only by the app itself, meaning other apps cannot access them. Files saved to an external storage public directory are world-readable/writeable, so they can be modified by other apps or users beyond the app's control.
According to Android developer documentation, “internal storage is best when you want to be sure that neither the user nor other apps can access your files.”
By contrast, “external storage is the best place for files that don't require access restrictions and for files that you want to share with other apps or allow the user to access with a computer.”
By default, WhatsApp stores media files received by a device in external storage, in the following path: /storage/emulated/0/WhatsApp/Media/. In Telegram, if a user enables the “Save to Gallery” feature, under the assumption that this is safe and without understanding its indirect ramifications, Telegram will similarly store files in: /storage/emulated/0/Telegram/. Both are public directories. The apps load the received files from the public directories for users to see in the chat interface, when they enter the relevant chat.The fact that files are stored in, and loaded from, external storage without proper security mechanisms (see more on this under “How app developers can protect against the threat” below), allows other apps with write-to-external storage permission to risk the integrity of the media files. Write-to-external storage (WRITE_EXTERNAL_STORAGE) is a common permission requested by Android apps, with over a million apps in Google Play having this access. In fact, based on our internal app data, we found nearly 50% of a given device’s apps have this permission.
Researchers showed how a malicious app could manipulate images, invoices and audio files by running in the background and monitoring the targeted messaging app for received files.
In particularly, the invoices manipulation scenario seems be really dangerous: the attacker could programmatically swap the bank account information in a file in order to trick the victim into sending money to another account:
In one of the most damaging Media File Jacking attacks, a malicious actor can manipulate an invoice sent by a vendor to a customer, to trick the customer into making a payment to an illegitimate account.
As in the previous scenario, an app that appears to be legitimate but is in fact malicious, watches for PDF invoice files received via WhatsApp, then programmatically swaps the displayed bank account information in the invoice with that of the bad actor.
The customer receives the invoice, which they were expecting to begin with, but has no knowledge that it’s been altered. By the time the trick is exposed, the money may be long gone.
To make matters worse, the invoice hack could be broadly distributed in a non-targeted way, looking for any invoices to manipulate, affecting multiple victims who use IM apps like WhatsApp to conduct business.
Is there a mitigation?
Symantec already notified Telegram and Facebook/WhatsApp about the Media File Jacking vulnerability: in the meantime a temporary mitigation can be the disabling of the feature that saves media files to external storage.
-
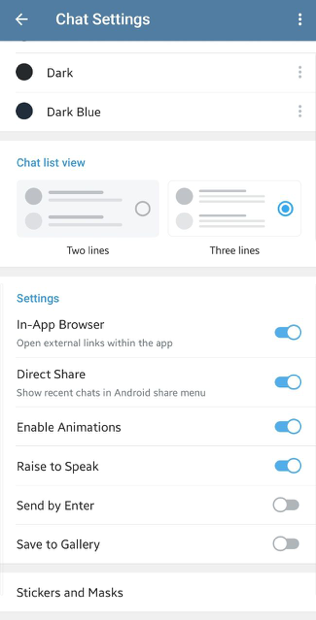
Telegram: Settings -> Chat Settings -> Save to Gallery -
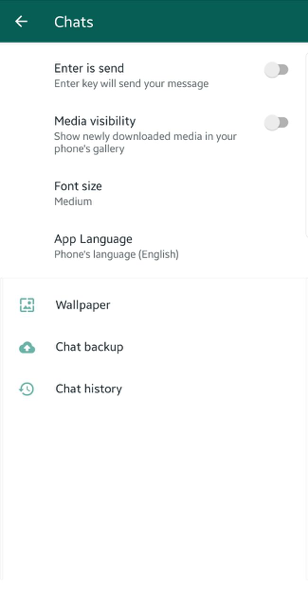
WhatsApp: Settings -> Chats -> Media Visibility
Telegram did not immediately respond to a request for comment. A WhatsApp spokesperson said changing its storage system would limit the service’s ability to share media files, and even introduce new privacy issues. “WhatsApp has looked closely at this issue and it’s similar to previous questions about mobile device storage impacting the app ecosystem,” the spokesperson said in a statement. “WhatsApp follows current best practices provided by operating systems for media storage and looks forward to providing updates in line with Android’s ongoing development.”