Forensic analysis of Windows 10 compressed memory using Volatility
Memory analysis on Windows 10 is pretty different from previous Windows versions: a new feature, called Memory Compression, make it necessary a forensic tool able to read compressed memory pages.
Windows 10 memory compression
Recent releases of Windows 10 include the memory compression feature, which is capable of reducing the memory usage by compressing some memory pages using the Xpress algorithm and storing them in the so-called compression store (these pages are decompressed back to their original form when they are needed).ut
Windows 10 memory compression is a significant evolution in the design of the memory manager: it increases system performance by making a more efficient use of physical memory, but is more complex than previous windows systems and is currently not publicly documented.
Analyzing Windows 10 memory dumps
Update 2020-12-20: this commit on Volatility GitHub repository could be useful!
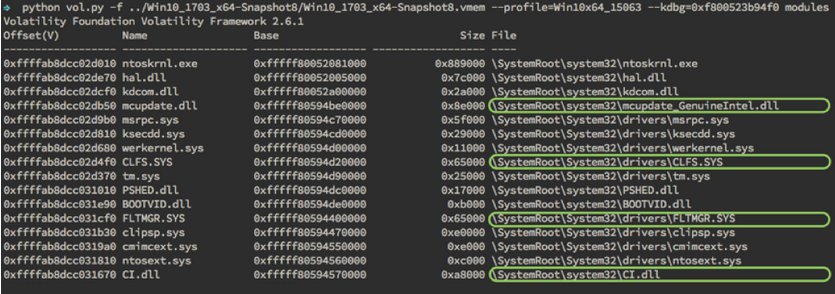
Standard version of Volatility is unable to inspect memory stored in compressed pages, leaving a lot of forensics artifacts undetected.
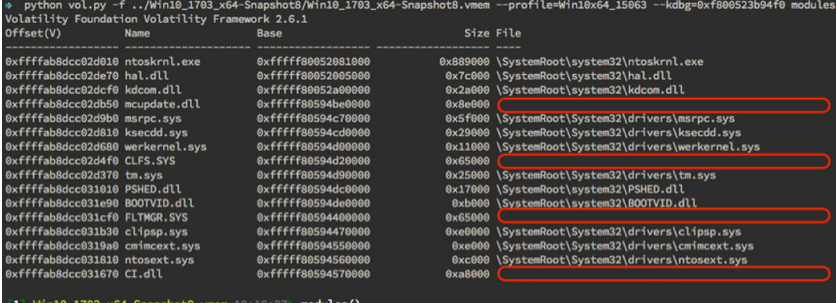
Fortunately, the FireEye's FLARE team created a custom version of volatility with specific changes for reading the compressed memory of Windows 10:
To enable a more complete memory analysis on Windows 10, FireEye’s FLARE team analyzed the operating system’s memory manager as well as the algorithms and structures used to retrieve compressed memory. The memory we’re looking for is stored in a virtual store, created by the Store Manager kernel component. The Store Manager is responsible for managing data involved in performance optimization systems, including SuperFetch, ReadyBoost, and ReadyDrive. In this case, the Virtual Store is a RAM-backed entity, leveraging storage space in MemCompression.exe for processes’ compressed data. The results of this research have been ported to both Volatility and Rekall to benefit the security community.
To deal with missing data due to compressed pages, FireEye's FLARE team made multiple additions to Volatility and Rekall to support Windows 10 memory compression. First and foremost, we added the necessary overlays
An overlay describes the internal data structures used by the Windows 10 memory compression algorithm and makes them available in Python. For example, the overlays define the layout of the SMKM_STORE structure and the B+Trees used to lookup compressed pages.
The undocumented Windows structures defined in the overlays are based on information we obtained through analyzing different versions of Windows 10. Being undocumented, these structures are susceptible to change across Windows builds, and even revisions. We currently support versions 1607, 1703, 1709, 1803, and 1809 on both 32-bit and 64-bit architectures. To support additional versions, the layout of the structures must be analyzed and the overlays updated accordingly.