Simjacker: a brand new mobile vulnerability exploited by surveillance companies for espionage operation
Some updates here!
Researchers from AdaptiveMobile Security have uncovered a new and previously undetected vulnerability and associated exploits, called Simjacker.
This vulnerability is currently being actively exploited by a specific private company that works with governments to monitor individuals. Simjacker and its associated exploits is a huge jump in complexity and sophistication compared to attacks previously seen over mobile core networks.
The main Simjacker attack involves a SMS containing a specific type of spyware-like code being sent to a mobile phone, which then instructs the SIM Card within the phone to ‘take over’ the mobile phone to retrieve and perform sensitive commands, exploiting the presence of a particular piece of software, called the S@T Browser on the SIM card.
During the attack, the user is completely unaware that they received the attack, that information was retrieved, and that it was successfully exfiltrated.
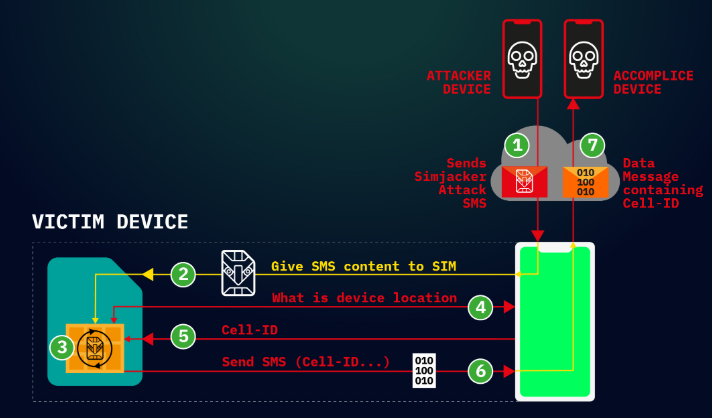
The attack begins when a SMS - that we term the Simjacker ‘Attack Message’ - is sent to the targeted handset.
This Simjacker Attack Message, sent from another handset, a GSM Modem or a SMS sending account connected to an A2P account, contains a series of SIM Toolkit (STK) instructions, and is specifically crafted to be passed on to the UICC/eUICC (SIM Card) within the device. In order for these instructions to work, the attack exploits the presence of a particular piece of software, called the S@T Browser - that is on the UICC.
Once the Simjacker Attack Message is received by the UICC, it uses the S@T Browser library as an execution environment on the UICC, where it can trigger logic on the handset.
For the main attack observed, the Simjacker code running on the UICC requests location and specific device information (the IMEI) from the handset.
Once this information is retrieved, the Simjacker code running on the UICC then collates it and sends the combined information to a recipient number via another SMS (we call this the ‘Data Message’), again by triggering logic on the handset.
This Data Message is the method by which the location and IMEI information can be exfiltrated to a remote phone controlled by the attacker.https://www.adaptivemobile.com/blog/simjacker-next-generation-spying-over-mobile
Why is this technique special?
The attack relies both on these specific SMS messages being allowed, and the S@T Browser software being present on the UICC in the targeted phone. Specific SMS messages targeting UICC cards have been demonstrated before on how they could be exploited for malicious purposes.
The Simjacker attack takes a different approach, and greatly simplifies and expands the attack by relying on the S@T Browser software as an execution environment. The S@T (pronounced sat) Browser – or SIMalliance Toolbox Browser to give it its full name – is an application specified by the SIMalliance, and can be installed on a variety of UICC (SIM cards), including eSIMs.
This S@T Browser software is not well known, is quite old, and its initial purpose was to enable services such as getting your account balance through the SIM card.
Globally, its function has been mostly superseded by other technologies, and its specification has not been updated since 2009, however, like many legacy technologies it is still been used while remaining in the background.
In this case we have observed the S@T protocol being used by mobile operators in at least 30 countries whose cumulative population adds up to over a billion people, so a sizable amount of people are potentially affected. It is also highly likely that additional countries have mobile operators that continue to use the technology on specific SIM cards.https://www.adaptivemobile.com/blog/simjacker-next-generation-spying-over-mobile
This technique allows attacker to retrieve user location, but also allows remote malicious users to execute STK commands, like:
- PLAY TONE
- SEND SHORT MESSAGE
- SET UP CALL
- SEND USSD
- SEND SS
- PROVIDE LOCAL INFORMATION
- Location Information, IMEI, Battery, Network, Language, etc
- POWER OFF CARD
- RUN AT COMMAND
- SEND DTMF COMMAND
- LAUNCH BROWSER
- OPEN CHANNEL
- CS BEARER, DATA SERVICE BEARER, LOCAL BEARER, UICC SERVER MODE, etc
- SEND DATA
- GET SERVICE INFORMATION
- SUBMIT MULTIMEDIA MESSAGE
- GEOGRAPHICAL LOCATION REQUEST
These command could be used by an attacker to fulfil such purposes as:
- Mis-information (e.g. by sending SMS/MMS messages with attacker controlled content)
- Fraud (e.g. by dialling premium rate numbers),
- Espionage (as well as the location retrieving attack an attacked device it could function as a listening device, by ringing a number),
- Malware spreading (by forcing a browser to open a web page with malware located on it)
- Denial of service (e.g by disabling the SIM card)
- Information retrieval (retrieve other information like language, radio type, battery level etc.)
AdaptiveMobile Security also released a useful briefing paper: https://simjacker.com/downloads/briefingpapers/AdaptiveMobile-Security_Simjacker-Briefing-Paper.pdf
Is there a fix?
Not yet, but AdaptiveMobile is working on this threat:
- We have been working with our own mobile operator customers to block these attacks, and we are grateful to their assistance in helping detect this activity.
- We also communicated to the GSM Association – the trade body representing the mobile operator community - the existence of this vulnerability. This vulnerability has been managed through the GSMA CVD program, allowing information to be shared throughout the mobile community.https://www.adaptivemobile.com/blog/simjacker-next-generation-spying-over-mobile
References
- https://simjacker.com/
- https://www.adaptivemobile.com/blog/simjacker-next-generation-spying-over-mobile
- https://portal.3gpp.org/desktopmodules/Specifications/SpecificationDetails.aspx?specificationId=1807
- https://simjacker.com/downloads/briefingpapers/AdaptiveMobile-Security_Simjacker-Briefing-Paper.pdf