BlackDirect: a vulnerability in Microsoft OAuth 2.0 may allows attackers to takeover Microsoft and Azure Accounts
Security researcher Omer Tsarfati from CyberArk has discovered [1] a vulnerability in Microsoft's OAuth implementation that may allows attacker to create authentication tokens with the victim’s permissions.
This could let a malicious attacker access and control a victim’s account and take actions on their behalf.
According with official website [2]:
The vulnerability exists within specific Microsoft-created Azure applications that trust unregistered URLs. Attackers can take ownership of these URLs which will allow them to use the victims’ permissions to hijack identity tokens. Once they have the identity tokens, the attacker can impersonate the victims and perform malicious actions on their behalf.
The vulnerable applications -- called “Enterprise Applications” in Azure use OAuth protocol and contain a list of URLs that are trusted. Since those URLs and subdomains are not registered by Microsoft, they can be registered by anyone (including an attacker). What makes the severity of this vulnerability so high is that those apps are approved by default in any Azure environment and have the permissions to get the users’ identity token – making it possible for the attacker to take over the victims’ accounts and perform actions using their permissions – including having access to Azure and Active Directory resources, Virtual Machines and more.
Researchers also published a video with a PoC of this technique:
Who is affected?
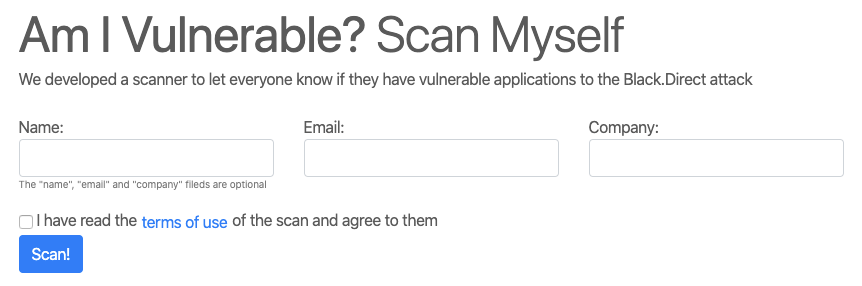
Anyone who has Microsoft or Azure accounts would be vulnerable to this kind of attack: researcher released a simple online tool (in homepage [2]) useful to check if your azure applications are vulnerable.
Is there a patch? And how can I protect myself against this attack?
According with researcher statement:
Following our report to Microsoft, the specific vulnerable URLs we discovered were fixed – eliminating their risk. However, there could be more vulnerable Azure applications in your environment which trust vulnerable URLs so we recommend you check the different applications that are being trusted in your Azure environment.
and, about mitigations:
1) Stay alert to Social Engineering attacks – this is how the attacker could convince potential victims to visit an infected website or click a link.
2) Surf only to legitimate websites that you trust
3) Disable unused applications
4) Make sure that all the trusted redirect URIs configured in the enterprise application are under your ownership and remove unnecessary redirect URIs
5) Make sure the permissions that the OAuth application asks for are the least privileged one it needs