My Weekly RoundUp #122
I know, last week I slacked off, so few interesting links.
Don't worry, few but good!
Cybersecurity
PoC exploits for Citrix ADC and Gateway CVE-2019-19781 flaw released online

Experts announced the availability online of proof-of-concept exploit code for CVE-2019-19781 flaw in Citrix NetScaler ADC and Citrix NetScaler Gateway servers.
While security researchers were warning of ongoing scans for Citrix Application Delivery Controller (NetScaler ADC) and Citrix Gateway (NetScaler Gateway) servers affected by the CVE-2019-19781 vulnerability, many experts are announcing the availability online of proof-of-concept exploit code ([1, 2]).
Researchers at MDSsec published technical details of the vulnerability along with a video that shows the exploit they have developed, but they decided to not release it to avoid miscreants use it in the wild.
PGP keys, software security, and much more threatened by new SHA1 exploit
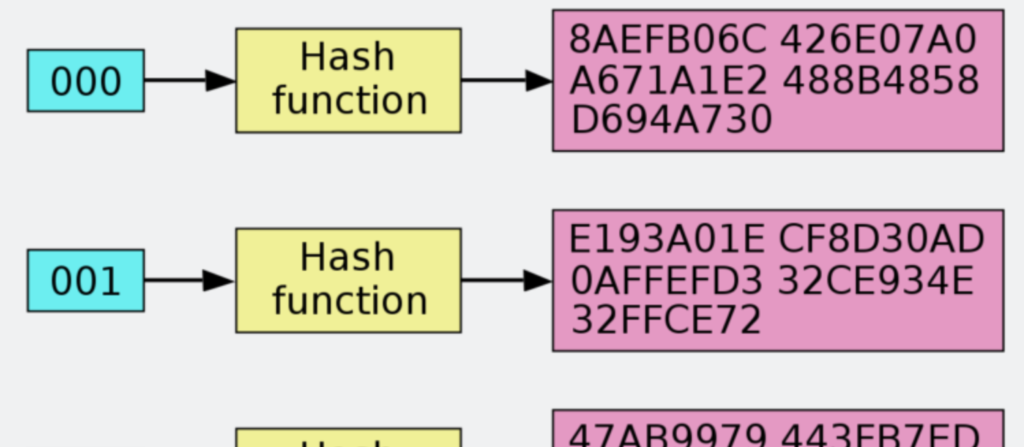
Three years ago, Ars declared the SHA1 cryptographic hash algorithm officially dead after researchers performed the world’s first known instance of a fatal exploit known as a "collision" on it. On Tuesday, the dead SHA1 horse got clobbered again as a different team of researchers unveiled a new attack that’s significantly more powerful.
The new collision gives attackers more options and flexibility than were available with the previous technique. It makes it practical to create PGP encryption keys that, when digitally signed using SHA1 algorithm, impersonate a chosen target. More generally, it produces the same hash for two or more attacker-chosen inputs by appending data to each of them. The attack unveiled on Tuesday also costs as little as $45,000 to carry out. The attack disclosed in 2017, by contrast, didn’t allow forgeries on specific predetermined document prefixes and was evaluated to cost from $110,000 to $560,000 on Amazon’s Web Services platform, depending on how quickly adversaries wanted to carry it out.
Why 2FA SMS is a Bad Idea

Two-factor authentication (2FA) brings an extra layer of security that passwords alone can’t provide. Requiring an extra step for a user to prove their identity reduces the chance of a bad actor gaining access to data.
One of the most common methods of 2FA is SMS text messages. The problem is that SMS is not a secure medium. Hackers have several tools in their arsenal that can intercept, phish, and spoof SMS. Despite this security flaw and better options for authentication, SMS-based 2FA is still used by several institutions.
Google's Zero Project: new disclosure policy
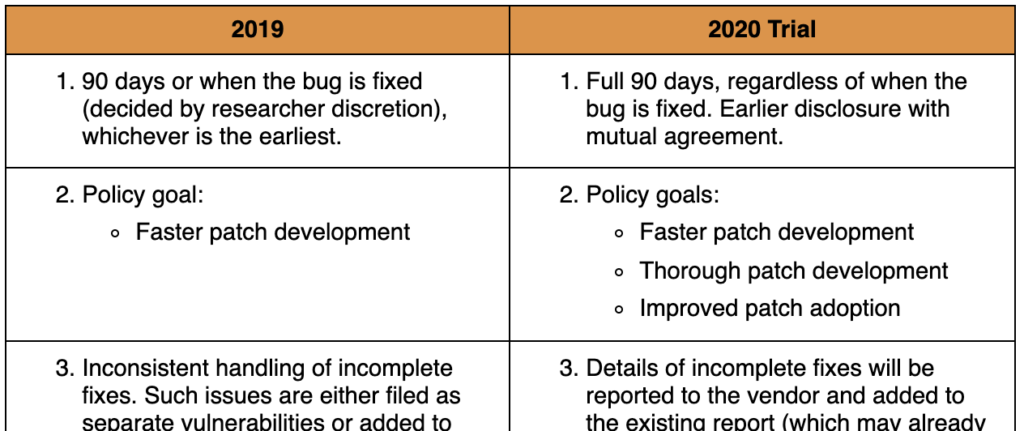
For vulnerabilities reported starting January 1, 2020, we are changing our Disclosure Policy: Full 90 days by default, regardless of when the bug is fixed. Fix a bug in 20 days? We will release all details on Day 90.Fix a bug in 90 days? We will release all details on Day 90.If there is mutual agreement between the vendor and Project Zero, bug reports can be opened to the public before 90 days elapse. For example, a vendor wants to synchronize the opening of our tracker report with their release notes to minimize user confusion and questions. We will try this policy for 12 months, and then consider whether to change it long term.
Blind SQL Injection without an “in”
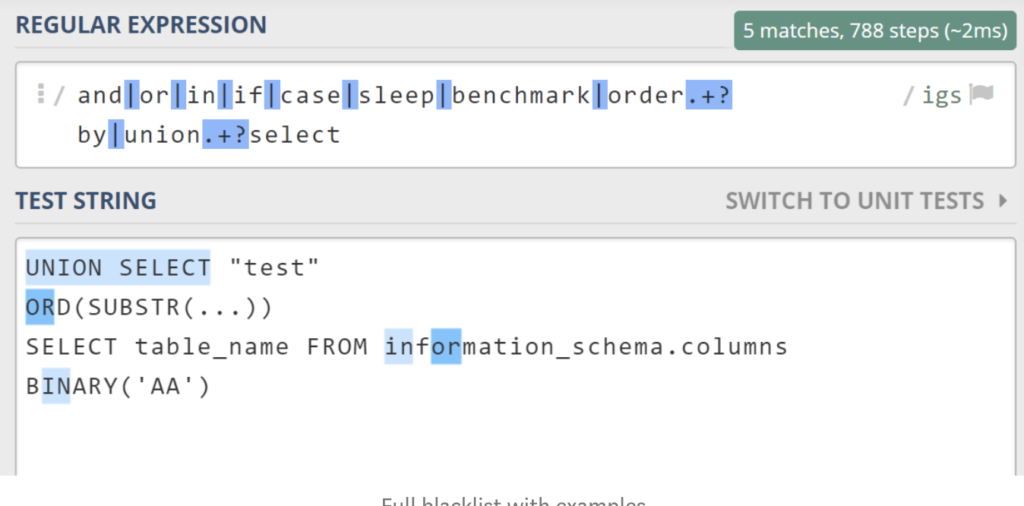
As for the sake of exercising, I looked up a few web challenges on TetCTF and noticed an interesting one — ”Secure System”.
The goal of the challenge was to craft a Blind SQL Injection payload without using:
- UNION … SELECT
- information_schema
- “in” and “or” keywordsAlthough the filter was way more complex, these were the hardest obstacles to overcome.
Programming
"How to build a PaaS for 1500 engineers"
Companies that reach a certain size typically create one or more teams that take care of different subsets of those tools. They get named something like “infrastructure”, “platform”, “foundations”… I will use “Platform team” in this text.
A good deal of the job is ultimately about finding the right balances between standardization and autonomy. To make meaningful impact, Platform teams depend on having standards in their organization. Trying to too support every possible language ecosystem, framework, DB, messaging system, and whatnot spreads Platforms teams too thin to be effective.
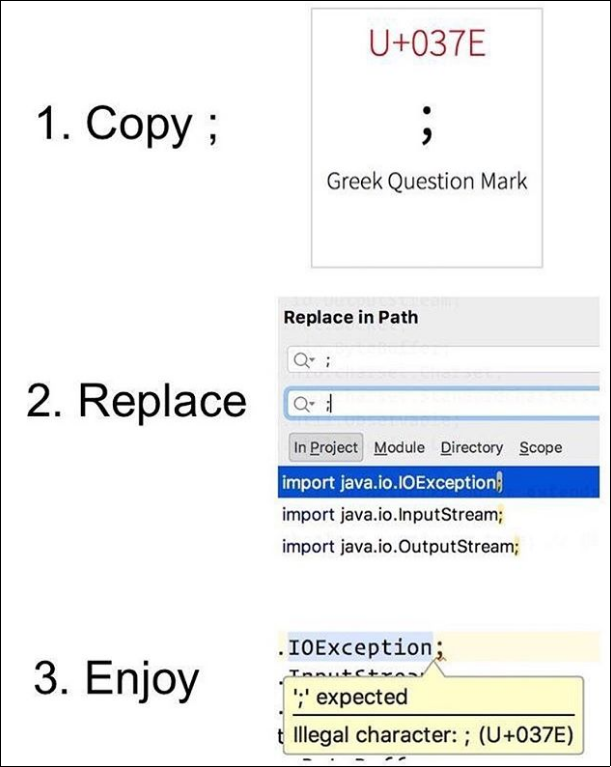
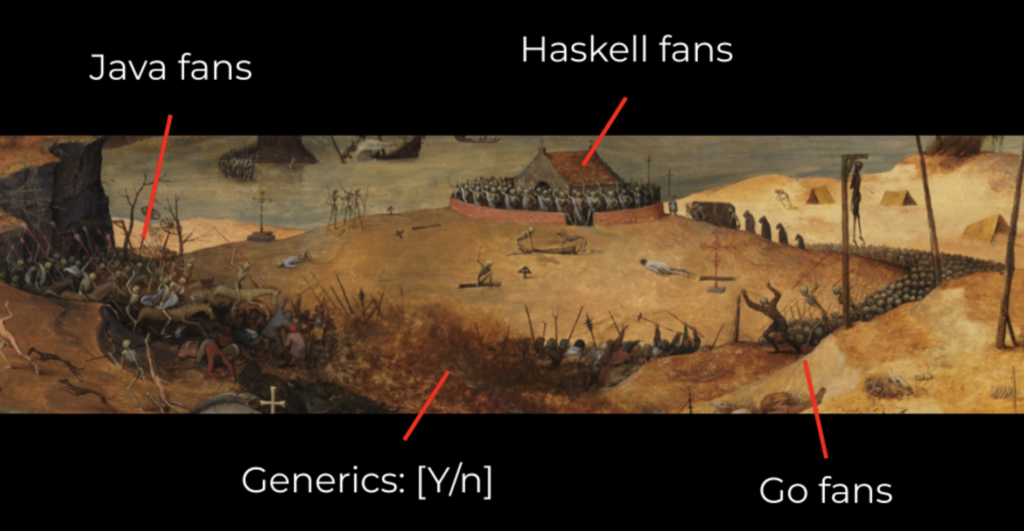
This person deserves to go to hell 😡 😭
HTML attributes to improve your users' two factor authentication experience
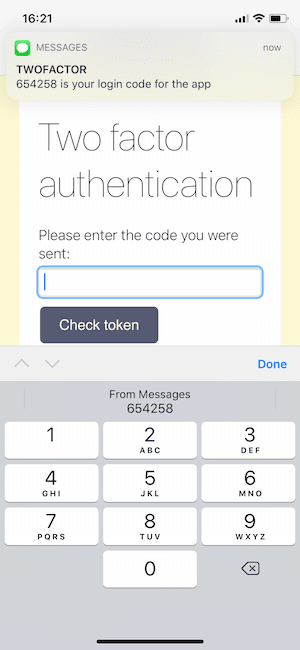
There are plenty of opportunities for friction in the user experience when logging in, particularly while entering a two factor authentication code. As developers we should be building applications that support the need for account security but don't detract from the user experience. Sometimes it can feel as though these requirements are in a battle against each other.
In this post we will look at the humble
<input>element and the HTML attributes that will help speed up our users' two factor authentication experience.
Privacy
Apple Is Scanning Your Photos

Apple's senior director of global privacy has confirmed that the company scans photos uploaded to the iCloud for evidence of illegal activities such as child sexual abuse.
Jane Horvath made the admission while speaking at the Consumer Electronics Show (CES) 2020 conference in Las Vegas yesterday, according to The Telegraph.
While speaking at the tech conference, Horvath said that photographs that are backed up to Apple's online storage service are automatically screened for illicit content.
The company has been criticized by law enforcement agencies for allowing criminals to hide behind lanes of protective encryption and for refusing to break into the phones of suspected wrongdoers.
Addressing this issue yesterday in Las Vegas, Horvath said that giving criminals nowhere to hide by scrapping encryption was "not the way we’re solving these issues" but added: "We are utilizing some technologies to help screen for child sexual abuse material."
Exactly what technologies Apple is using to screen their customers' digital photographs and how long they have been doing so was not specified.
Entertainment
BIRDS OF PREY – Official Trailer
Gotham’s worst brings out their best. Meet Harley Quinn, Black Canary, Huntress, Renee Montoya, and Cassandra Cain.
Top 10 Best Chewbacca Quotes

Making a list of the top Chewbacca quotes from Star Wars was so difficult because there are so many great ones, but here are ten of our favorites!