TLDR #2: Cross-Site Request Forgery
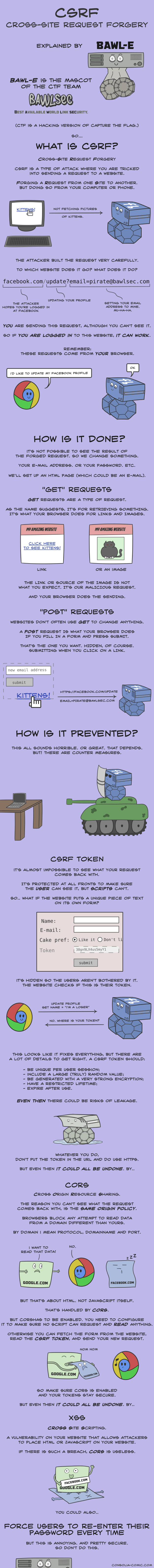
Cross-Site Request Forgery (CSRF) is a type of attack that allows a malicious web site, email, blog, instant message, or program to causes a user’s web browser to perform an unwanted action on a trusted site, when the user is authenticated.
This attack works because browser requests may automatically include any credentials associated with the site, such as the user’s session cookie or IP address: so, if the user is authenticated, the site cannot distinguish between the forged or legitimate request sent by the victim.
This infographic by Consolia Comics perfectly explains the process:
Also this video by PwnFunction is pretty useful:
Preventing CSRF attacks
The best way to avoid CSRF attacks is to include a CSRF token within relevant requests.
A CSRF token is a unique, secret and unpredictable value that is generated by the server and transmitted to the client in such a way that it is included in a subsequent HTTP request made by the client: the server will use this token in order to validate the request, and will generate another token….and so on!