The "distroless" approach to Docker containers
Most Docker images build on full Linux distributions often containing a lot of unnecessary complexity, adversely affecting also the application security.
However, by using Google’s “distroless” approach we can build small and secured runtime images.
Containerizing Apps, not VMs
The talk dates from 2017, however is still actual.
The traditional approaches to using docker containers are generally very different from the approach taken by the tech giants: while it’s easy to use base images you find on DockerHub to produce an app image, it leads to large images often with 98% extraneous files and unused components.
In this talk [1] at swampUP 2017, Matthew Moore will demonstrate a different approach to building Docker containers: using its open source Bazel [2] build system, Google aims to containerize just the app, and not the whole operating system.
Practical (and security) implications of small Docker images
The effort of keeping docker images as small as possible has, in my opinion, interesting implications:
- Less attack surface: limiting the amount of unused tool and files in the image, you can make the application more secure by restricting its capabilities to the bare minimum it needs to do its job.
- Less stuff to keep track of: every tool in an image is another thing that needs to be tracked and which needs to be scanned for known vulnerabilities.
- Less data to move: pull a big image is also an expense in the form of time and data transfer costs. It may not be that big effort from personal workstation, but if we’re talking about a 50-node Kubernetes cluster things can get pretty expensive.
How to deal with distroless images
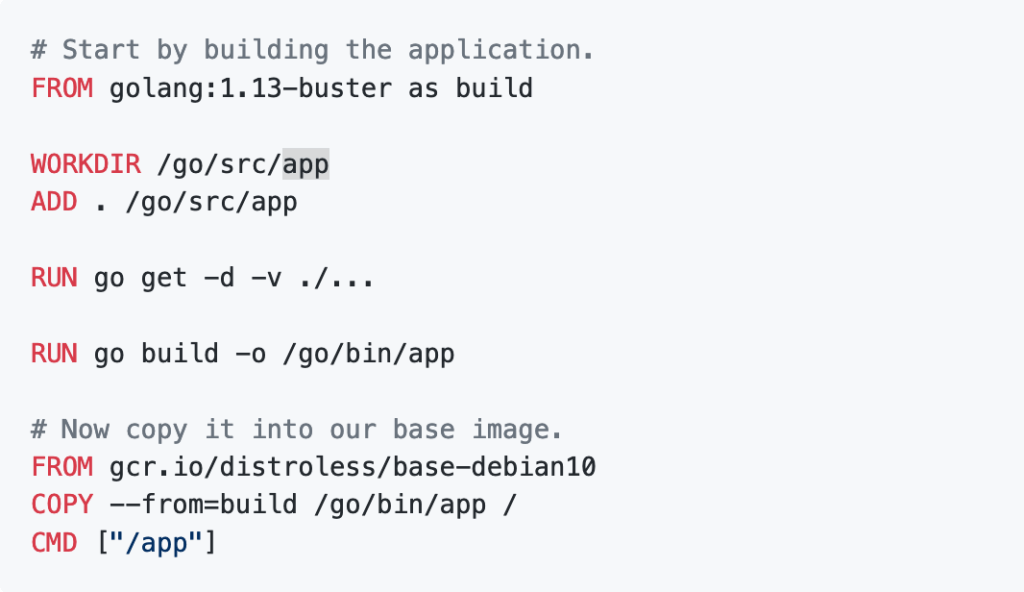
Rather than taking the top-down approach of trying to produce the smallest possible distro, the distroless images are built by adding only the dependencies and language runtimes absolutely necessary to run the application.
Google's method to build this kind of images taking advantage of some features of Bazel [2]: for a tutorial and technical informations, please refer to the github repo GoogleContainerTools/distroless [3], that also contains a lot of examples in Go, Java, Python, Python 3, Node.js and dotnet.