How to boot an Encase (E01) image using VirtualBox
Sometimes, during an incident analysis, you may need to replicate behaviours of a specific host, perhaps already acquired with a forensic method.
In order to perform this test, you first need to create a VM starting from a forensic image, so today wee se how to convert an Encase (E01) image into a file that can be read from VirtualBox [1].
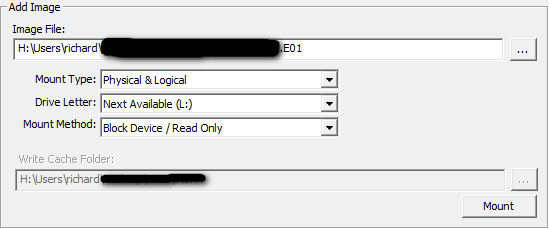
First, mount the .E01 image using FTK Imager [2] and give it a write cache:
Then you need to create a .VMDK file from the mounted image file, using this command (with high privileges):
vboxmanage.exe internalcommands createrawvmdk -filename "C:\SomePath\somefile.vmdk" -rawdisk \\.\PhysicalDrive2
(replace PhysicalDrive2 with drive mounted with FTK)
The command creates a .VMDK pointer to the mounted image file.
You can now create a machine within virtual box, give it the right OS and add the .VMDK pointer in as the HDD. and try to boot the system.
If the system show a BSOD, you can try to change the controller from SATA to IDE within the Virtual Machine settings. Then try changing the drop down controller box to ICH6. Further, if the system is UEFI you will have to check the UEFI box.