Android Triage: a really useful forensic tool by Mattia Epifani
Most of forensic acquisition activities on an Android device can be accomplished using the ADB (Android Debug Bridge) tool.
However, a lot of commands are required: luckily, the forensic expert Mattia Epifani created a bash script that automatize a lot of operations needed to collect device informations.
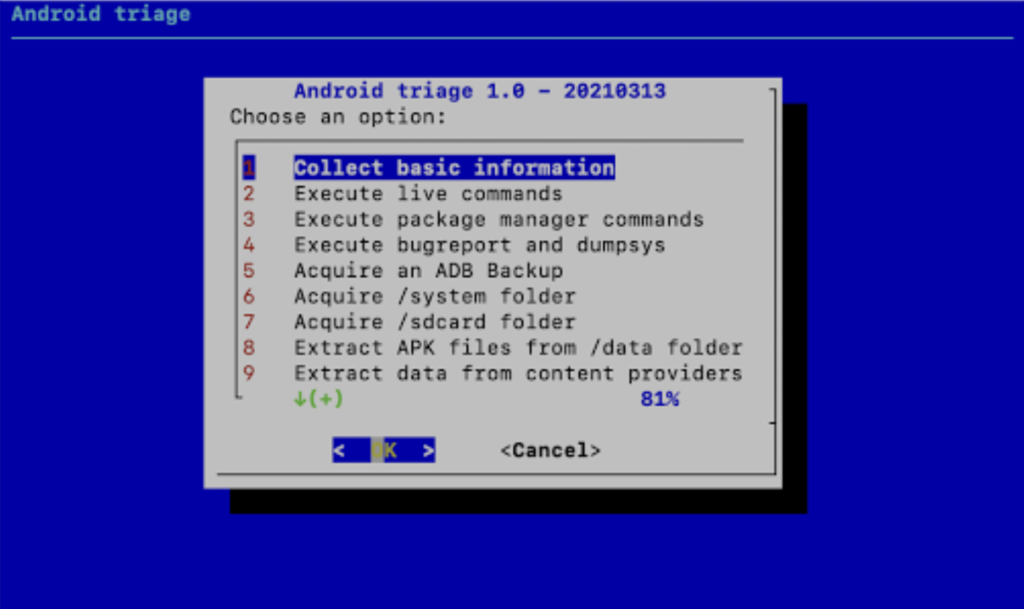
The tool, called “android_triage” [1], is a simple bash script that leverages ADB at its maximum level.
On the ADB side, most of the commercial tools use four methods:
- ADB Backup: the tool executes the "adb backup" command, with some possible variations among the different tools. This typically doesn't include native and third-party apps data: every single app can specify in the AndroidManifest file (android:allowBackup parameter) if its data should be included or not in an ADB backup. An Android Backup typically includes the sdcard (emulated storage) content and some native databases
- Agent: the tool installs an agent (basically, an APK file) that requests permissions to read native application data, in particular Contacts, Call Log, and SMS/MMS. After GDPR, Google changed its permissions policy and introduced a restriction in reading call log and SMS only to the default handler: this required some changes in the flow used by most forensics tools
- ADB Screenshot: the tool leverages the ADB feature that allows taking a screenshot of the device. In this way, also third-party apps can be "screenshotted" and then processed in the tool, by using some image analysis techniques, to parse the content and make it readable and searchable
- APK Downgrade: the tool uninstalls the actual version of a third-party package (app) by preserving user data, and installs a previous version of the same package where the android:allowBackup parameter is set to "true". The tool creates an ADB Backup that includes the specific app and then reinstalls the actual app version.
The Android Debug Bridge is, in reality, more powerful than this, as it allows us to obtain a shell without root privileges. In this shell you can run commands (both Linux-native and Android-specific) and pull files and folders from the device(where root privileges are not required).
Requirements
- ADB (https://developer.android.com/studio/releases/platform-tools)
- dialog (for Mac OS X see here http://macappstore.org/dialog/)
How to use it
- Activate ADB on the Android Device
- Connect and pair the Android Device and the host
- Make the script executable (chmod +x android_triage.sh)
- Execute the script and follow the instructions