Recognize and avoid IMSI-catchers with Android IMSI Catcher Detector
“ You are being watched!”
The Android-IMSI-Catcher-Detector (short: AIMSICD) is an Android open-source based project to detect and avoid fake base stations (IMSI-Catchers) or other base-stations (mobile antennas) with poor/no encryption, born in 2012 on XDA.
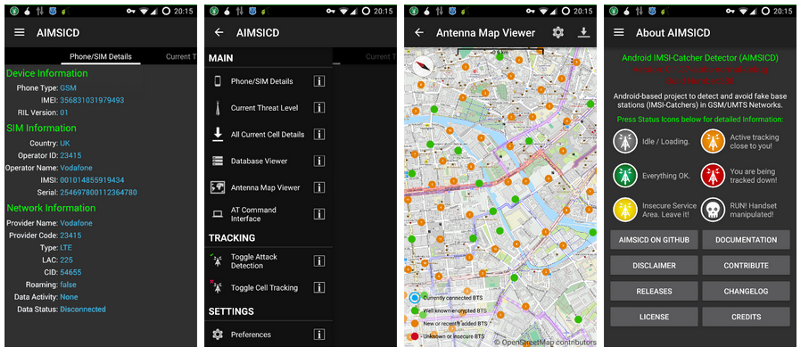
The project aims to warn the user if the ciphering is turned off on your phone, if the device has been tracked via Silent/Stealth SMS and also enable several protection mechanisms.
What is an IMSI-catcher?
An IMSI-catcher is a telephone eavesdropping device used for intercepting mobile phone traffic and tracking movement of mobile phone users.
Essentially consist of a “fake” mobile tower acting between the target mobile phone and the service provider’s real towers with a man-in-the-middle (MITM) attack.

IMSI-catchers are used in some countries by law enforcement and intelligence agencies, but their use has raised significant civil liberty and privacy concerns and is strictly regulated in some countries. Furthermore, some countries do not even have encrypted phone data traffic or uses a very weak encryption, thus rendering an IMSI-catcher unnecessary.
The IMSI-Catchers are so commonly used, are very easy to using and they leave no traces.
The police can deploy IMSI-Catchers to obtain data from of everyone holding a cell phone, determinating their location or finding out who is in a given geographic area at what time.
Also identity thieves can use freely available tools and even build their own fake GSM BTS to monitor and manipulate communications, notably for stealing passwords or credit card data from people nearby who make purchases on their phones.
Here a video of the speech “Defending mobile phones“ by Karsten Nohl and Luca Melette recorded at the 28th Chaos Communication Congress (December 2011):
[embed]https://www.youtube.com/watch?v=YWdHSJsEOck[/embed]
Silent SMS?
Also known as Type0-SMS, the Silent SMS uses an invisible return signal, or “ping” that allows the user to send a message to another mobile without the knowledge of the recipient mobile’s owner.
The message is rejected by the recipient mobile, and leaves no trace. In return, the sender gets a message from a mobile operator confirming that the Silent SMS has been received.
This kind of SMS were originally intended to allow operators to ascertain whether a mobile phone is switched on and to “test” the network, without alerting the users.
But now, intelligence services and police have found some other uses for the system: a user can be located by identifying the three antennas closest to his mobile, then triangulating the distance according to the speed it takes for a signal to make a return trip.
A mobile phone updates its presence on the network regularly, but when the person moves, the information is not updated immediately.
By sending a Silent SMS, the location of the mobile is instantly updated. This is very useful because it allows you to locate someone at a given time, and this technique is much more effective than a simple cellular location (Cell ID).
Application Goals
- Detect IMSI based device location tracking
- Detect and prevent the use of false BTS towers used for illegal interception
- Detect and prevent the use of broken ciphering algorithms (A5/1) during calls
- Detect and prevent remote hidden application installation
- Detect and prevent remote hidden SMS-based SIM attacks
- Provide counter measures against tracking
- Prevent leakage of sensitive GPS data
- Provide swarm-wise-decision-based cellular service interruption
- Provide secure wifi/wimax alternative data routes through MESH-like networking
- Aims to be recommended and added to the Guardian Project’s list of secure Apps
- Aims to be recommended by the SSD Project of the Electronic Frontier Foundation
- Aims to be recommended by Privacy International (and like-minded organizations)