New version of FinFisher spyware used to spy on iOS and Android users in 20 countries
Malware researchers from Kaspersky have discovered new and improved versions of the FinFisher spyware, able o infect both Android and iOS devices.
According to the experts, the new versions have been active at least since 2018, one of the samples analyzed was used last month in Myanmar, where local government is accused of violating human rights.
Kaspersky said this week the notorious commercial spyware, developed by Gamma Group and sold by its subsidiary Gamma International to allegedly respectable governments, has been showing up in the wild since late last year, most recently in a group of devices located in Myanmar this June.
While FinSpy, also known as FinFisher, has been touted as mobile device surveillanceware as far back as 2012, the Kaspersky research team said this latest version is particularly invasive in its ability to collect user chats, physical movements, and stored files from a wide range of applications. The new code been spotted in 20 countries, with the actual reach likely being much greater, it is claimed.https://www.theregister.co.uk/2019/07/11/finspy_snoopware_update/
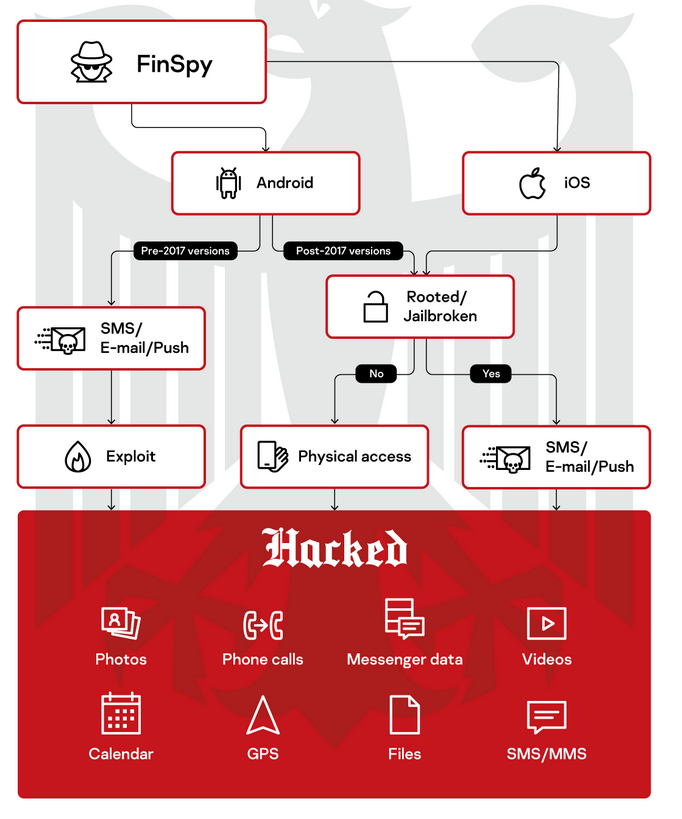
Android and iOS versions use different infection techniques
FinSpy for iOS does not provide infection exploits for its customers. An attacker could jailbreak the device if it has physical access to it.
For jailbroken devices, the attackers could use SMS message, email, and WAP Push as an infection vector:
FinSpy for iOS is able to monitor almost all device activities, including record VoIP calls via external apps such as Skype or WhatsApp. The targeted applications include secure messengers such as Threema, Signal and Telegram.
However, functionality is achieved by leveraging Cydia Substrate’s hooking functionality, so this implant can only be installed on jailbroken devices (iPhone or iPad; iPod has not been confirmed) compatible with iOS 11 and below (newer versions are not confirmed as at the time of the research and implants for iOS 12 has not been observed yet).
After the deployment process, the implant provides the attacker with almost unlimited monitoring of the device’s activities.The analyzed implant contained binary files for two different CPU architectures: ARMv7 and ARM64. Taking into account that iOS 11 is the first iOS version that does not support ARMv7 any more, we presumed that the 64-bit version was made to support iOS 11+ targets.
It looks like FinSpy for iOS does not provide infection exploits for its customers, because it seems to be fine-tuned to clean traces of publicly available jailbreaking tools. Therefore, an attacker using the main infection vector will need physical access in order to jailbreak it.
For jailbroken devices, there are at least three possible infection vectors:
- SMS message
- WAP Push
Any of those can be sent from the FinSpy Agent operator’s terminal.https://securelist.com/new-finspy-ios-and-android-implants-revealed-itw/91685/
The Android version is also capable of gaining root privileges on an unrooted device by exploiting the DirtyCow exploit:
The Android implant has similar functionality to the iOS version, but it is also capable of gaining root privileges on an unrooted device by abusing the DirtyCow exploit, which is contained in the malware.
FinSpy Android samples have been known for a few years now. Based on the certificate data of the last version found, the sample was deployed in June 2018.
The Android implant’s functionality is unlikely to change much, based on the fact that most of the configuration parameters are the same in the old and new versions. The variety of available settings makes it possible to tailor the behavior of the implant for every victim. For example, operators can choose the preferred communication channels or automatically disable data transfers while the victim is in roaming mode.
All the configuration data for an infected Android device (including the location of the control server) is embedded in the implant and used afterwards, but some of the parameters can be changed remotely by the operator.
The configuration data is stored in compressed format, split into a set of files in the assets directory of the implant apk. After extracting all pieces of data and building the configuration file, it’s possible to get all the configuration values. Each value in the configuration file is stored after the little-endian value of its size, and the setting type is stored as a hash.https://securelist.com/new-finspy-ios-and-android-implants-revealed-itw/91685/
How FinSpy gets on the device and what it steals
Overall, during the research, up-to-date versions of these implants used in the wild were detected in almost 20 countries. However, assuming the size of Gamma’s customer base, it’s likely that the real number of victims is much higher.
FinSpy developers are constatly working on the updates for their malware. At the time of publication, Kaspersky researchers have found another version of the threat and are currently investigating this case.https://securelist.com/new-finspy-ios-and-android-implants-revealed-itw/91685/