Some thoughts about Browser Fingerprinting
Browser fingerprinting is an incredibly accurate method of tracking online activity but, luckily, there are a few things you can do to try to wipe your fingerprints.
TL;DR
Are you a privacy obsessed? Don't use an unusual browser!
What is browser fingerprinting?
Browsers don't behave the same way when presented with the same webpage: some elements could be rendered improperly or positioned at the wrong location.
In order to mitigate this problem, browsers started including the “user agent” header that informed the server on the browser being used so that it could send the device a page that was optimized for it, starting the era of the “Best on IE” or “Optimized for Netscape.”
Today the user-agent header is still used but a different purpose.
Now the web is a platform full of features, that allow to listen to music, watch videos and so on, and can also use a very wide variety of devices from tablets, smartphones or laptops.
To get the best optimized experience, devices needs to share a lot of configuration information with the server, like timezone, OS version, model of graphic card etc…
However, all that information used to optimize the user experience can be also collected to build a browser fingerprint.
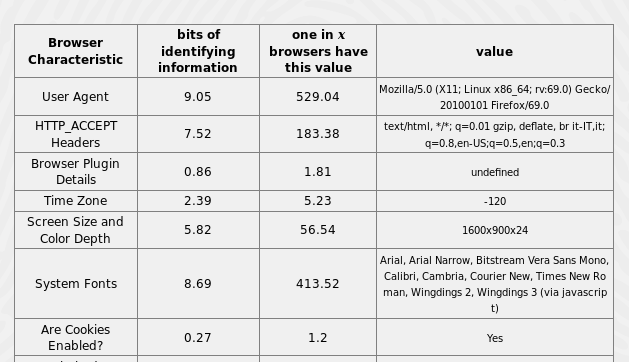
If you want to see your own browser fingerprint, try to visit AmIUnique.org: with the information collected via received HTTP headers and via JavaScript it is able to create a unique signature for your browser.
In this example, the site is able to collect:
On this website, we collect:
- the User agent header
- the Accept header
- the Connection header
- the Encoding header
- the Language header
- the Upgrade Insecure Requests header
- the Referer header
- the Cache-Control header
- the BuildId of the browser
- the list of plugins
- the platform
- the cookies preferences (allowed or not)
- the Do Not Track preferences (yes, no or not communicated)
- the timezone
- the screen resolution and its color depth
- the use of local storage
- the use of session storage
- a picture rendered with the HTML Canvas element
- a picture rendered with WebGL
- Supported Audio formats
- Supported Video formats
- the presence of AdBlock
- the list of fonts
Why browser fingerprinting is a threat to online privacy?
There is no need to ask for permissions to collect all this information and any script running in your browser can silently build a fingerprint of your device without you even knowing about it.
Furthermore with fingerprint your device can be identified and tracked online without need for a cookie, avoid privacy extensions that block tracking cookies.
How to defend against browser fingerprinting?
There are some defensive measures that can be taken with existing browsers, and for day-to-day use the best option is to run tools like Privacy Badger or Disconnect that will block some (but not all) of the domains that try to perform fingerprinting.
Actually, the most realistic protection is using the Tor Browser, but also a tool like NoScript can reduces the amount of data available to fingerprinters.
The most obvious way: use a "non-rare" browser
A simple way to try to prevent browser fingerprinting is to pick a "common" browser, for example the latest version of Chrome running on a modern Windows version.
But even so, many of those Chrome on Windows browsers can be distinguished from one another by the enormous range of plugin versions and fonts that can be installed with them, so some other protection methods need to be used
Using an Ad Blocker
Common adblocking tools tend to be quite good at blocking ads, because users can instantly see when they're present.
Tracking or fingerprinting scripts are generally invisible, so even if users enable features that focus on privacy, some trackers may still slip past the net.
Using NoScript
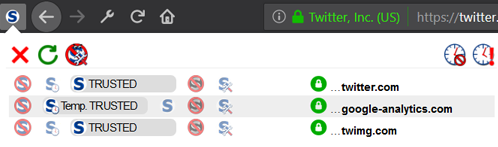
Disabling JavaScript is a powerful defense against browser fingerprinting, because it cuts off the methods used to detect plugins and fonts, as well as preventing the use of most kinds of supercookie. Unfortunately, JavaScript is necessary to make a lot of sites work well, so a sort of 'intelligent blocking' is needed.
NoScript may help us: it will block JavaScript everywhere and allow you to manually reenable it for some sites.
This is a lot of work, and requires good intuitions about when a site isn't working because JavaScript is disabled: is a power-user tool than a solution for everyone.
Using Tor Browser
Tor Browser has has been configured to "standardize" various browser characteristics like the User Agent string, in order to prevent them from being used to track Tor users.
In response to various fingerprinting experiments (like Panopticlick or AmIUnique), Tor Browser now includes patches to prevent font fingerprinting (by restricting which fonts websites can use) and Canvas fingerprinting (by detecting reads to HTML5 Canvas objects and asking users to approve them).
Tor Browser can also be configured to aggressively block JavaScript using NoScript.
Taken together, these measures make the Tor Browser a strong defense against fingerprinting.